# CVE-2017-0213
# to get privilege Administator from CMD
### Vulnerable
| Product | Version | Update | Tested |
| :------------------ | :------ | :----- | :----- |
| Windows 10 | | | √ |
| Windows 10 | 1511 | | |
| Windows 10 | 1607 | | |
| Windows 10 | 1703 | | √ |
| Windows 7 | | SP1 | √ |
| Windows 8.1 | | | |
| Windows RT 8.1 | | | |
| Windows Server 2008 | | SP2 | |
| Windows Server 2008 | R2 | SP1 | |
| Windows Server 2012 | | | |
| Windows Server 2012 | R2 | | |
| Windows Server 2016 | | | |
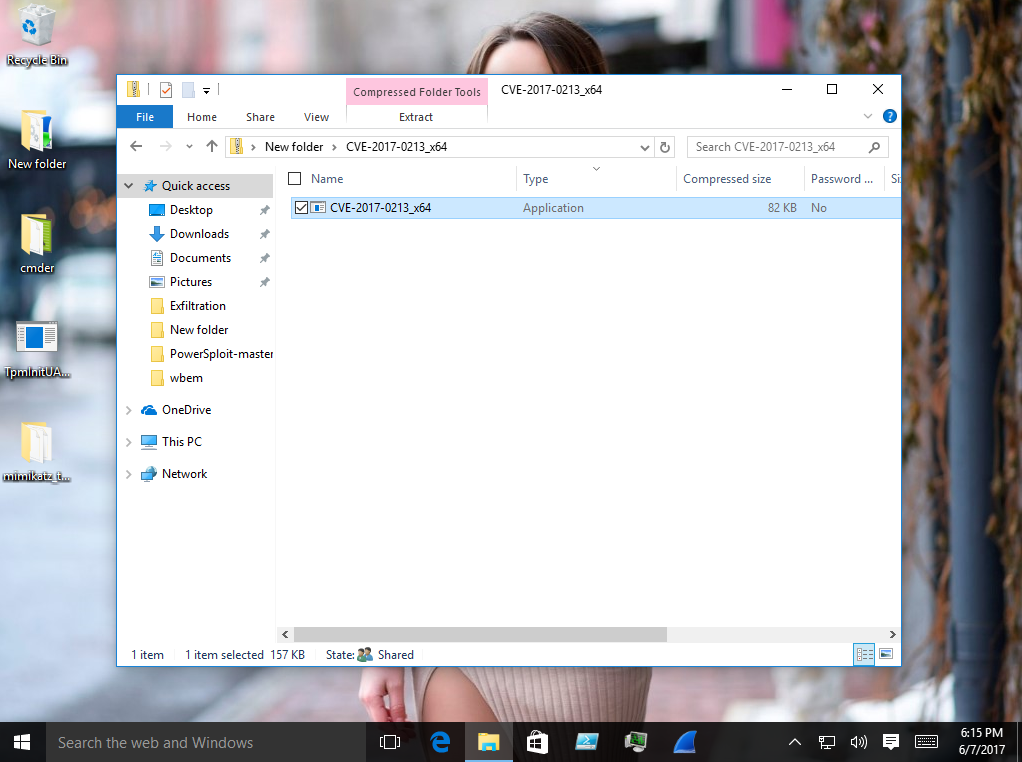
# 1
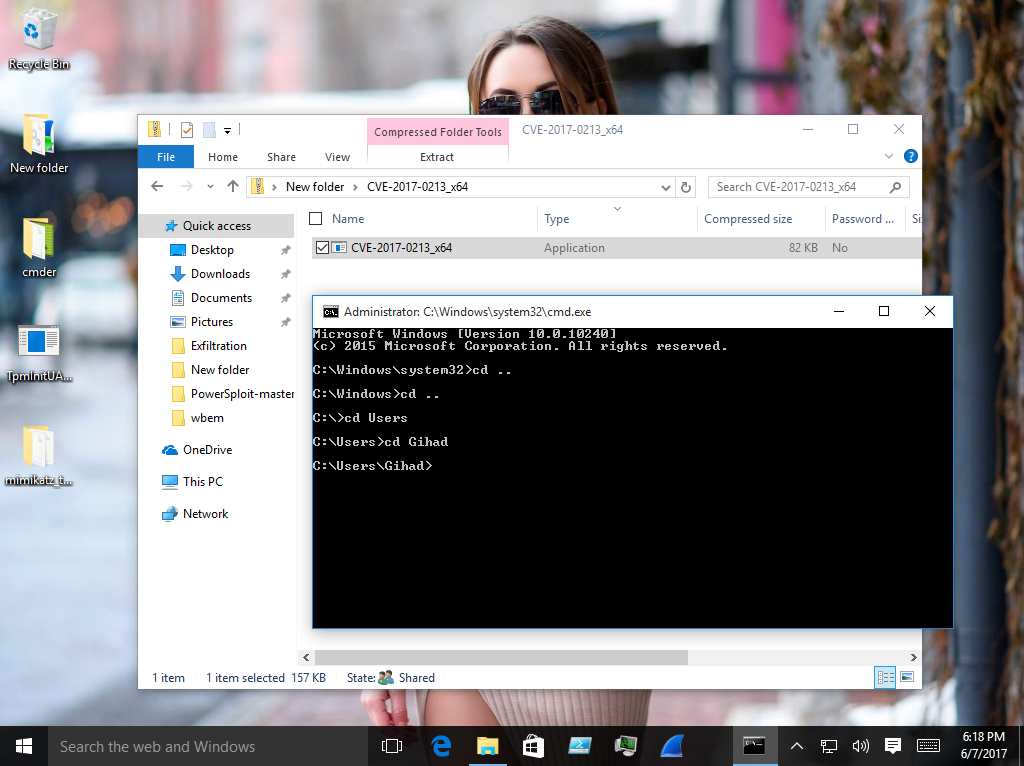
# 2
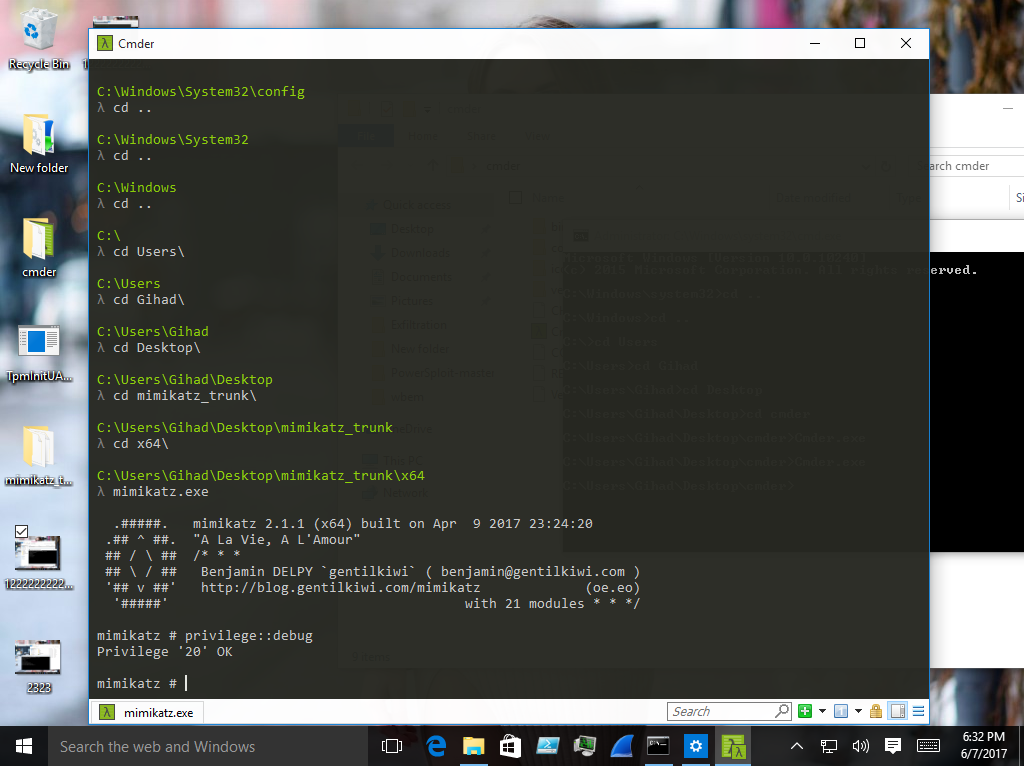
# use Mimikatz CVE-2017-0213
# But do not use On cmd Administator
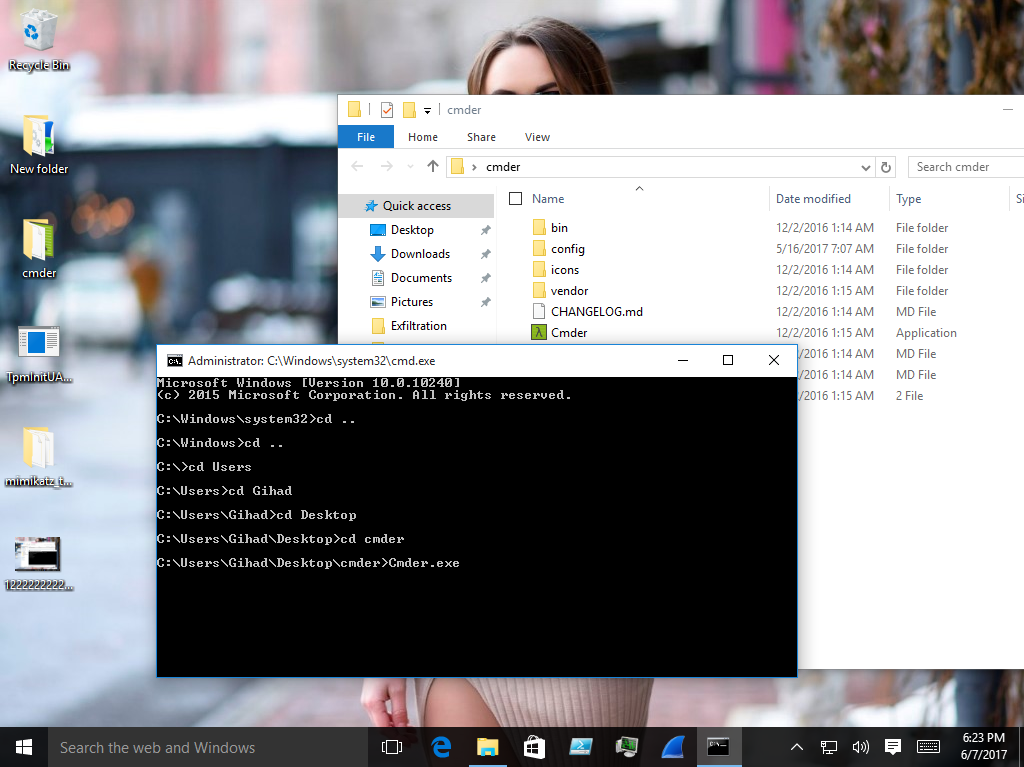
# But On Prject Cmder !
# Download Cmder !
# http://cmder.net/
# After the download
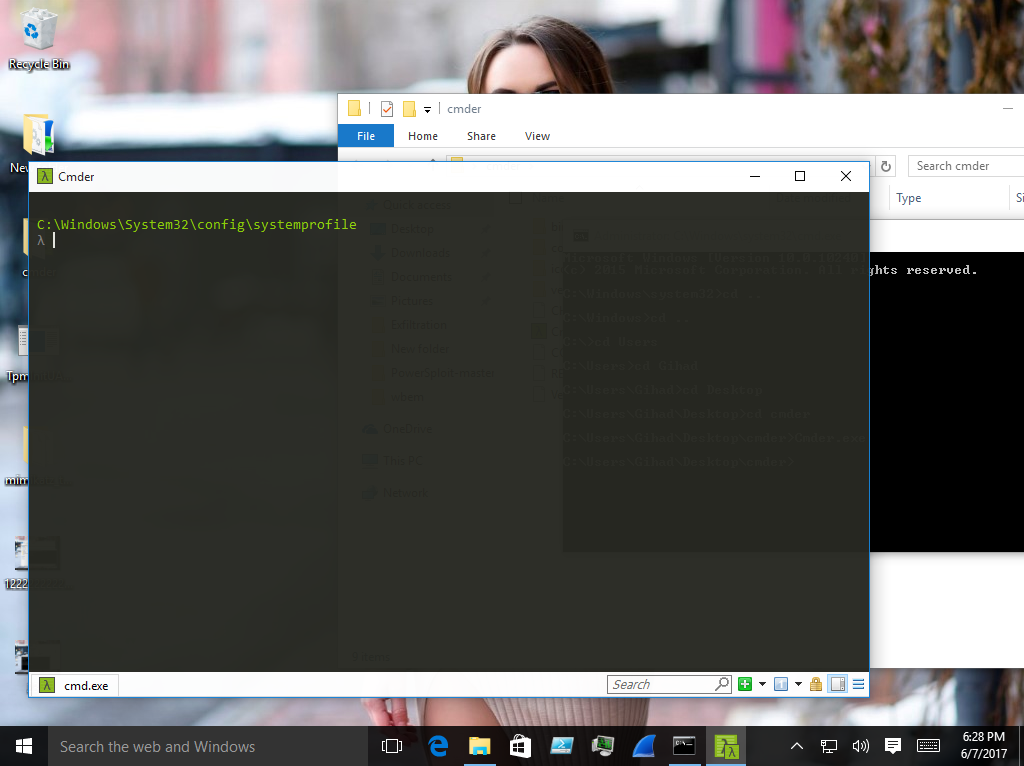
# Turn on Cmder from CVE-2017-0213 And then run Mimikatz On Cmder
# Some pictures !
# 1
# 2
# 3
**Video:** [Youtube](https://www.youtube.com/watch?v=Y_lTfhhgppE&t=1s)
[4.0K] /data/pocs/b175b0cd1e86562bb13ae205e31354826548fdf2
├── [157K] CVE-2017-0213_x64.exe
├── [132K] CVE-2017-0213_x86.exe
└── [1.7K] README.md
0 directories, 3 files