CVE-2023-42442# CVE-2023-42442
CVE-2023-42442 JumpServer Session 录像任意下载漏洞
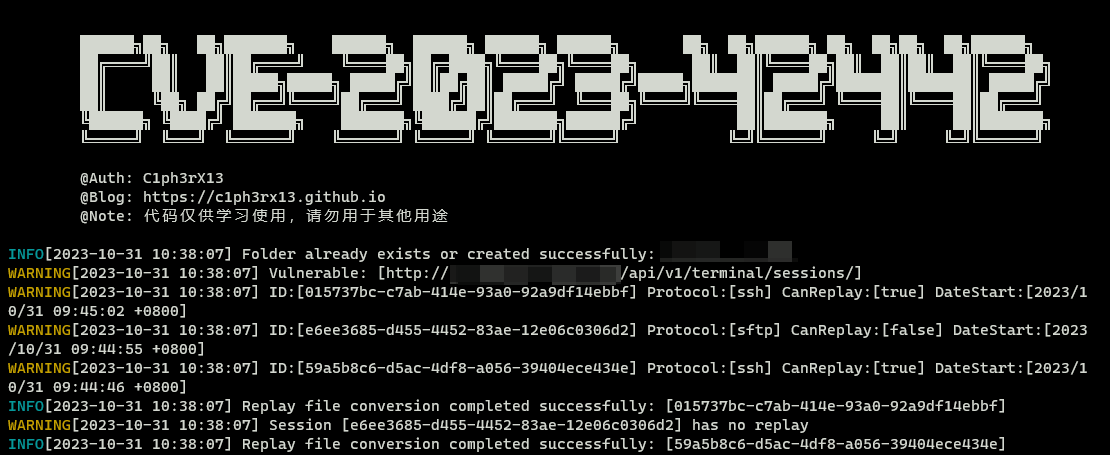
## 漏洞说明
CVE-2023-42442是一个组合洞,包含Jumpserver中的两个Bug
1. API未授权访问导致泄露session信息
2. 目录权限绕过导致录像文件被下载
## USAGE
### Python Version
```python
python CVE-2023-42442.py -h
██████╗██╗ ██╗███████╗ ██████╗ ██████╗ ██████╗ ██████╗ ██╗ ██╗██████╗ ██╗ ██╗██╗ ██╗██████╗
██╔════╝██║ ██║██╔════╝ ╚════██╗██╔═████╗╚════██╗╚════██╗ ██║ ██║╚════██╗██║ ██║██║ ██║╚════██╗
██║ ██║ ██║█████╗█████╗ █████╔╝██║██╔██║ █████╔╝ █████╔╝█████╗███████║ █████╔╝███████║███████║ █████╔╝
██║ ╚██╗ ██╔╝██╔══╝╚════╝██╔═══╝ ████╔╝██║██╔═══╝ ╚═══██╗╚════╝╚════██║██╔═══╝ ╚════██║╚════██║██╔═══╝
╚██████╗ ╚████╔╝ ███████╗ ███████╗╚██████╔╝███████╗██████╔╝ ██║███████╗ ██║ ██║███████╗
╚═════╝ ╚═══╝ ╚══════╝ ╚══════╝ ╚═════╝ ╚══════╝╚═════╝ ╚═╝╚══════╝ ╚═╝ ╚═╝╚══════╝
@Auth: C1ph3rX13
@Blog: https://c1ph3rx13.github.io
@Note: 代码仅供学习使用,请勿用于其他用途
usage: CVE-2023-42442.py [-h] -t TARGET
CVE-2023-42442 by C1ph3rX13.
options:
-h, --help show this help message and exit
-t TARGET, --target TARGET
target url
```

### Go Version
Build
```powershell
# 源码编译,暂时只支持Windows
go mod init CVE-2023-42442
go mod tidy
go build -ldflags="-s -w" -trimpath -o CVE-2023-42442.exe .\CVE-2023-42442.go
```
Run
```powershell
.\CVE-2023-42442.exe -h
██████╗██╗ ██╗███████╗ ██████╗ ██████╗ ██████╗ ██████╗ ██╗ ██╗██████╗ ██╗ ██╗██╗ ██╗██████╗
██╔════╝██║ ██║██╔════╝ ╚════██╗██╔═████╗╚════██╗╚════██╗ ██║ ██║╚════██╗██║ ██║██║ ██║╚════██╗
██║ ██║ ██║█████╗█████╗ █████╔╝██║██╔██║ █████╔╝ █████╔╝█████╗███████║ █████╔╝███████║███████║ █████╔╝
██║ ╚██╗ ██╔╝██╔══╝╚════╝██╔═══╝ ████╔╝██║██╔═══╝ ╚═══██╗╚════╝╚════██║██╔═══╝ ╚════██║╚════██║██╔═══╝
╚██████╗ ╚████╔╝ ███████╗ ███████╗╚██████╔╝███████╗██████╔╝ ██║███████╗ ██║ ██║███████╗
╚═════╝ ╚═══╝ ╚══════╝ ╚══════╝ ╚═════╝ ╚══════╝╚═════╝ ╚═╝╚══════╝ ╚═╝ ╚═╝╚══════╝
@Auth: C1ph3rX13
@Blog: https://c1ph3rx13.github.io
@Note: 代码仅供学习使用,请勿用于其他用途
Usage of CVE-2023-42442.exe:
-proxy string
Proxy Url: http/https://IP:Port
-t string
Target Url
```
### 更新日志
+ 2023-10-31 优化 Go Version,减少代码量
### 问题
+ `httpx`会自动化规范输入`url`的格式,即使是使用`Writing custom transports`
+ httpx wiki:https://www.python-httpx.org/advanced/#writing-custom-transports
+ `requests`则不会
### 参考
部分代码参考以下项目:
https://github.com/tarimoe/blackjump
## 免责声明
1. 本工具仅面向拥有合法授权的渗透测试安全人员及进行常规操作的网络运维人员,用户可在取得足够合法授权且非商用的前提下进行下载、复制、传播或使用。
2. 在使用本工具的过程中,您应确保自己的所有行为符合当地法律法规,且不得将此软件用于违反中国人民共和国相关法律的活动。本工具所有作者和贡献者不承担用户擅自使用本工具从事任何违法活动所产生的任何责任。
[4.0K] /data/pocs/a062abf3e2c161e40ad1ed3f37d06123fb091038
├── [5.7M] CVE-2023-42442.exe
├── [ 11K] CVE-2023-42442.go
├── [8.9K] CVE-2023-42442.py
├── [4.0K] images
│ ├── [ 52K] CVE-2023-42442.png
│ └── [ 56K] Go-CVE-2023-42442.png
├── [1.0K] LICENSE
└── [5.6K] README.md
1 directory, 7 files