Support x86 and x64# CVE-2017-8464-EXP
Support x86 and x64
Just for test
Lnk file from:
https://github.com/rapid7/metasploit-framework/pull/8767
Thanks to ykoster
Small change,replace the dll file,fix the bug of crashing explorer.exe.(ykoster has fixed this bug)
POC:
x86:
x64:
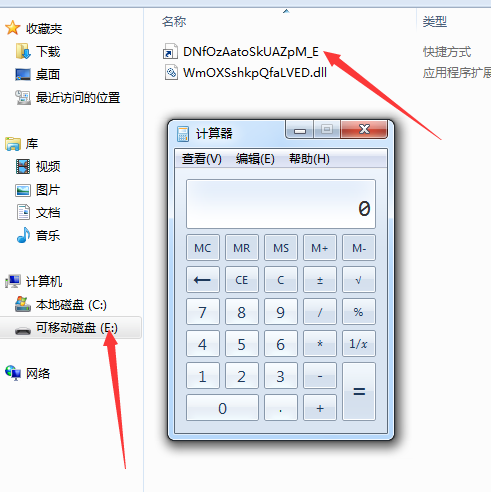
If you can determine the USB drive,one LNK file is enough,like this:
More details:
https://3gstudent.github.io/Windows-Lnk%E8%BF%9C%E7%A8%8B%E4%BB%A3%E7%A0%81%E6%89%A7%E8%A1%8C%E6%BC%8F%E6%B4%9E(CVE-2017-8464)%E5%88%A9%E7%94%A8%E6%B5%8B%E8%AF%95
[4.0K] /data/pocs/7939cc1b12210baf469f89a9e0f332ab3fda9e91
├── [4.0K] calc x64
│ ├── [ 240] bzimVhTxVSVAvqWW_H.lnk
│ ├── [ 240] CJqsRymyTEMnBoEC_T.lnk
│ ├── [ 240] emeDxGEdARUmzHYN_X.lnk
│ ├── [ 240] FavqRrpXeqruoJwm_M.lnk
│ ├── [ 240] gBsceXqQIqhXHySi_N.lnk
│ ├── [ 240] gzTXwmTukBDryAPx_L.lnk
│ ├── [ 240] hRAVeKFdQFfUWWqf_D.lnk
│ ├── [ 240] joJczkptYQtfkMNm_J.lnk
│ ├── [ 240] juHLixrdaEoaGDcL_I.lnk
│ ├── [ 240] laTnMsKakEOKsJHf_R.lnk
│ ├── [ 240] LdhMQIbWZpcSeVNj_Z.lnk
│ ├── [ 240] lvdfRmNKdkMexTNn_G.lnk
│ ├── [ 240] NfMIupIogETQsWra_V.lnk
│ ├── [ 49K] OuWZjtdbLqFVMSLF.dll
│ ├── [ 240] QZwHXICgEbiMtEwe_S.lnk
│ ├── [ 240] TeNENqdfbnkTNers_O.lnk
│ ├── [ 240] TFjoAQJOJqTTlynz_W.lnk
│ ├── [ 240] TpzgiaCNXaSnzlKx_K.lnk
│ ├── [ 240] TywZFloXXLcMoUVP_P.lnk
│ ├── [ 240] VhfYGmTcCCcrfTaY_Y.lnk
│ ├── [ 240] vnvlkoVTAEtCfPYX_Q.lnk
│ ├── [ 240] xWiOFoWnpbAxeKSr_U.lnk
│ ├── [ 240] YSfBenPxsQHppZuM_E.lnk
│ └── [ 240] ZMLUEPWbhtajeFvU_F.lnk
├── [4.0K] calc x86
│ ├── [ 240] AIGrEPvEOTXqjEaw_O.lnk
│ ├── [ 240] aQRlCerEgjVIRYLQ_N.lnk
│ ├── [ 240] cRTvZQMkUULYLGmW_F.lnk
│ ├── [ 240] DNfOzAatoSkUAZpM_E.lnk
│ ├── [ 240] FNqWxGJfjXHWtsOf_S.lnk
│ ├── [ 240] fXtYTHUBPuuoBWrl_P.lnk
│ ├── [ 240] gXRyeJymkCbmiXIR_H.lnk
│ ├── [ 240] gyhbcKquCWLSOUSd_U.lnk
│ ├── [ 240] iWYfETBuIkffMlgp_Z.lnk
│ ├── [ 240] lHGRXkTVRihDzkjl_R.lnk
│ ├── [ 240] lPfkoJiWxgsoSrsD_V.lnk
│ ├── [ 240] LqFWHUlZTWlULatC_G.lnk
│ ├── [ 240] MkGTeIIFLYOjZclX_I.lnk
│ ├── [ 240] nChCLwgSBXaEiwIR_Q.lnk
│ ├── [ 240] qIeuxAOnUEVJWOEe_K.lnk
│ ├── [ 240] QjcZPYwkZKEVQvgs_W.lnk
│ ├── [ 240] rxTDIbsrdXcyLvYA_Y.lnk
│ ├── [ 240] SAmbRRbbdmzXwBQm_J.lnk
│ ├── [ 240] SDtTgoPxAguJyxBw_T.lnk
│ ├── [ 240] sHEofvMNSNPGPxnI_X.lnk
│ ├── [ 240] uZfBVEFQdlRgsvpT_D.lnk
│ ├── [ 240] wDxKJhyBflVPXlwA_L.lnk
│ ├── [3.0K] WmOXSshkpQfaLVED.dll
│ └── [ 240] xXIRjCUwUvcECnmO_M.lnk
├── [1.5K] LICENSE
├── [ 52K] poc1.png
├── [ 789] README.md
├── [751K] x64.gif
└── [750K] x86.gif
2 directories, 53 files