# ssh_enum_users_CVE-2018-15473
Script que se aprovecha de la vulnerabilidad CVE-2018-15473 para enumerar usuarios.

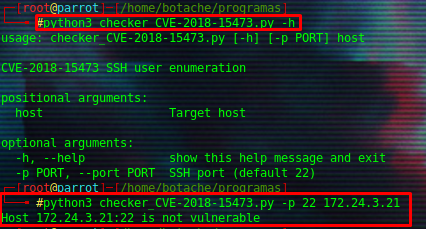
# Checker para CVE-2018-15473
Script para ver si el objetivo es vulnerable o no a CVE-2018-15473.
[4.0K] /data/pocs/782390dabaf36ab7875fc72b626cec1e05c172cc
├── [1.1K] checker_CVE-2018-15473.py
├── [ 436] README.md
└── [1.4K] ssh_enum_users2.py
0 directories, 3 files