Cisco Adaptive Security Appliance (ASA)/Firepower Threat Defense (FTD) - Local File Inclusion
<div align="center">
<img src="https://blogs.cappriciosec.com/uploaders/CVE-2020-3452-tool.png" alt="logo">
</div>
## Badges
[](https://choosealicense.com/licenses/mit/)



<a href="https://github.com/Cappricio-Securities/CVE-2020-3452/releases/"><img src="https://img.shields.io/github/release/Cappricio-Securities/CVE-2020-3452"></a>
[](https://twitter.com/cappricio_sec)
<p align="center">
<p align="center">
## License
[MIT](https://choosealicense.com/licenses/mit/)
## Installation
1. Install Python3 and pip [Instructions Here](https://www.python.org/downloads/) (If you can't figure this out, you shouldn't really be using this)
- Install via pip
- ```bash
pip install CVE-2020-3452
```
- Run bellow command to check
- `CVE-2020-3452 -h`
## Configurations
2. We integrated with the Telegram API to receive instant notifications for vulnerability detection.
- Telegram Notification
- ```bash
CVE-2020-3452 --chatid <YourTelegramChatID>
```
- Open your telegram and search for [`@CappricioSecuritiesTools_bot`](https://web.telegram.org/k/#@CappricioSecuritiesTools_bot) and click start
## Usages
3. This tool has multiple use cases.
- To Check Single URL
- ```bash
CVE-2020-3452 -u http://example.com
```
- To Check List of URL
- ```bash
CVE-2020-3452 -i urls.txt
```
- Save output into TXT file
- ```bash
CVE-2020-3452 -i urls.txt -o out.txt
```
- Want to Learn about [`CVE-2020-3452`](https://blogs.cappriciosec.com/cve/163/Cisco(CVE-2020-3452))? Then Type Below command
- ```bash
CVE-2020-3452 -b
```
<p align="center">
<b>🚨 Disclaimer</b>
</p>
<p align="center">
<b>This tool is created for security bug identification and assistance; Cappricio Securities is not liable for any illegal use.
Use responsibly within legal and ethical boundaries. 🔐🛡️</b></p>
## Working PoC Video
[](https://asciinema.org/a/OUyUI01vgWvWgvizXrpA1IDbm)
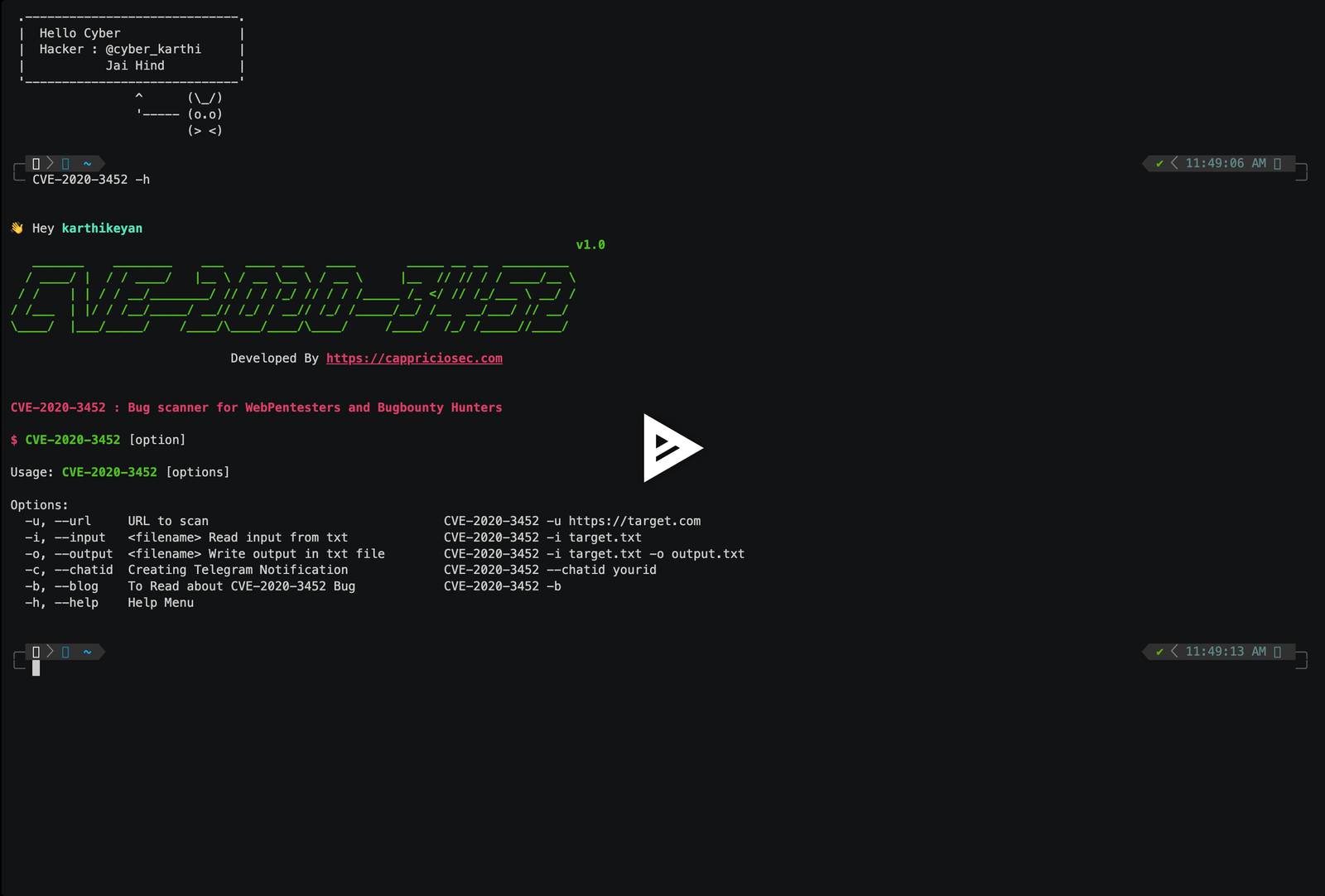
## Help menu
#### Get all items
```bash
👋 Hey Hacker
v1.0
_______ ________ ___ ____ ___ ____ _____ __ __ _________
/ ____/ | / / ____/ |__ \ / __ \__ \ / __ \ |__ // // / / ____/__ \
/ / | | / / __/________/ // / / /_/ // / / /_____ /_ </ // /_/___ \ __/ /
/ /___ | |/ / /__/_____/ __// /_/ / __// /_/ /_____/__/ /__ __/___/ // __/
\____/ |___/_____/ /____/\____/____/\____/ /____/ /_/ /_____//____/
Developed By https://cappriciosec.com
CVE-2020-3452 : Bug scanner for WebPentesters and Bugbounty Hunters
$ CVE-2020-3452 [option]
Usage: CVE-2020-3452 [options]
```
| Argument | Type | Description | Examples |
| :-------- | :------- | :------------------------- | :------------------------- |
| `-u` | `--url` | URL to scan | CVE-2020-3452 -u https://target.com |
| `-i` | `--input` | filename Read input from txt | CVE-2020-3452 -i target.txt |
| `-o` | `--output` | filename Write output in txt file | CVE-2020-3452 -i target.txt -o output.txt |
| `-c` | `--chatid` | Creating Telegram Notification | CVE-2020-3452 --chatid yourid |
| `-b` | `--blog` | To Read about CVE-2020-3452 Bug | CVE-2020-3452 -b |
| `-h` | `--help` | Help Menu | CVE-2020-3452 -h |
## 🔗 Links
[](https://cappriciosec.com/)
[](https://www.linkedin.com/in/karthikeyan--v/)
[](https://twitter.com/karthithehacker)
## Author
- [@karthithehacker](https://github.com/karthi-the-hacker/)
## Feedback
If you have any feedback, please reach out to us at contact@karthithehacker.com
[4.0K] /data/pocs/4543a30f7f1c99aa5156b58a478be0eebbb06359
├── [4.0K] cve20203452
│ ├── [4.0K] includes
│ │ ├── [ 647] bot.py
│ │ ├── [ 468] filereader.py
│ │ ├── [ 0] __init__.py
│ │ ├── [2.2K] scan.py
│ │ └── [ 283] writefile.py
│ ├── [1.7K] main.py
│ └── [4.0K] utils
│ ├── [1.9K] configure.py
│ ├── [ 927] const.py
│ ├── [2.3K] helpers.py
│ ├── [ 0] __init__.py
│ └── [ 227] status.py
├── [1.0K] LICENSE
├── [4.6K] README.md
└── [ 991] setup.py
3 directories, 14 files