Identifying and Mitigating the CVE-2020–0796 flaw in the fly# Identifying and Mitigating the CVE-2020–0796 flaw in the fly
CVE-2020–0796, is pre-remote code execution vulnerability that resides in the Server Message Block 3.0 (SMBv3) network communication protocol, which Microsoft will not address the issue as the part of the March 2020 Tuesday.
## Usage
`python3 cve-2020-0796-scanner.py IP`
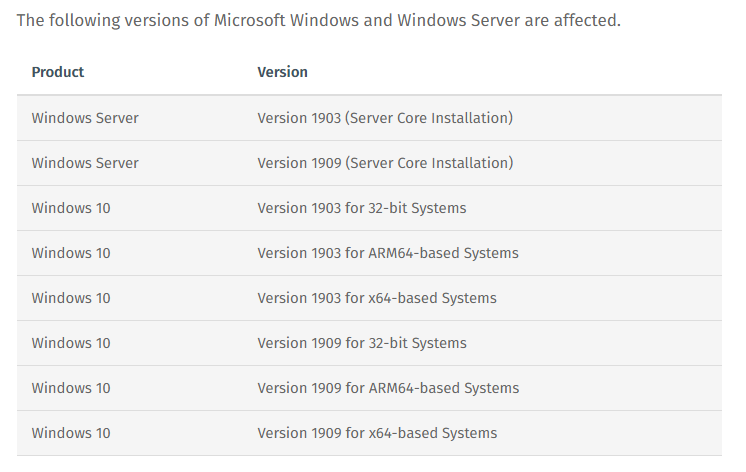
## Which devices does the CVE-2020-0796 affect?
## Packet request negotiate on the SMB protocol

For further information on the vulnerability how to mitigate it check the post of mine in; https://medium.com/@butrintkomoni/identifying-and-mitigating-the-cve-2020-0796-flaw-in-the-fly-7f2404ebe979
[4.0K] /data/pocs/1be20638726565caadf7a3bb2635b5c05159699a
├── [1.1K] cve-2020-0796-scanner.py
└── [ 773] README.md
0 directories, 2 files